About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 19 results common-pool clear search
Agent-based Modelling of Unsustainable and Sustainable Norms Under Resource Constraints
Fachrizal Sinaga Adrian Thomas Sufyan Fawwad | Published Monday, November 24, 2025This model explores the coupled dynamics of social norm diffusion and finite resource depletion. Extending the “Affordance Landscape” framework by Kaaronen & Strelkovskii (2020), this simulation investigates how resource scarcity and regeneration rates influence the adoption of pro-environmental behaviours.
The model addresses the gap by linking behavioural norms to a depleting common-pool resource. It tests whether sustainable norms can diffuse rapidly enough to prevent ecological collapse and identifies “tipping points” where resource scarcity acts as a driver for behavioural change.
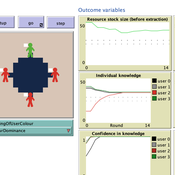
The purpose of the study is to unpack and explore a potentially beneficial role of sharing metacognitive information within a group when making repeated decisions about common pool resource (CPR) use.
We explore the explanatory power of sharing metacognition by varying (a) the individual errors in judgement (myside-bias); (b) the ways of reaching a collective judgement (metacognition-dependent), (c) individual knowledge updating (metacognition- dependent) and d) the decision making context.
The model (AgentEx-Meta) represents an extension to an existing and validated model reflecting behavioural CPR laboratory experiments (Schill, Lindahl & Crépin, 2015; Lindahl, Crépin & Schill, 2016). AgentEx-Meta allows us to systematically vary the extent to which metacognitive information is available to agents, and to explore the boundary conditions of group benefits of metacognitive information.
Communication and Trust in a Commons Dilemma Experiment
Marco Janssen | Published Sunday, October 02, 2022An agent model is presented that aims to capture the impact of cheap talk on collective action in a commons dilemma. The commons dilemma is represented as a spatially explicit renewable resource. Agent’s trust in others impacts the speed and harvesting rate, and trust is impacted by observed harvesting behavior and cheap talk. We calibrated the model using experimental data (DeCaro et al. 2021). The best fit to the data consists of a population with a small frequency of altruistic and selfish agents, and mostly conditional cooperative agents sensitive to inequality and cheap talk. This calibrated model provides an empirical test of the behavioral theory of collective action of Elinor Ostrom and Humanistic Rational Choice Theory.
Peer reviewed Multilevel Group Selection I
Wayne W. Wakeland Thaddeus Shannon Garry Sotnik | Published Tuesday, April 21, 2020 | Last modified Saturday, July 03, 2021New theoretical agent-based model of population-wide adoption of prosocial common-pool behavior with four parameters (initial percent of adopters, pressure to change behavior, synergy from behavior, and population density); dynamics in behavior, movement, freeriding, and group composition and size; and emergence of multilevel group selection. Theoretical analysis of model’s dynamics identified six regions in model’s parameter space, in which pressure-synergy combinations lead to different outcomes: extinction, persistence, and full adoption. Simulation results verified the theoretical analysis and demonstrated that increases in density reduce number of pressure-synergy combinations leading to population-wide adoption; initial percent of contributors affects underlying behavior and final outcomes, but not size of regions or transition zones between them; and random movement assists adoption of prosocial common-pool behavior.
Port of Mars simplified
Marco Janssen | Published Tuesday, January 14, 2020This is a simulation model to explore possible outcomes of the Port of Mars cardgame. Port of Mars is a resource allocation game examining how people navigate conflicts between individual goals and common interests relative to shared resources. The game involves five players, each of whom must decide how much of their time and effort to invest in maintaining public infrastructure and renewing shared resources and how much to expend in pursuit of their individual goals. In the game, “Upkeep” is a number that represents the physical health of the community. This number begins at 100 and goes down by twenty-five points each round, representing resource consumption and wear and tear on infrastructure. If that number reaches zero, the community collapses and everyone dies.
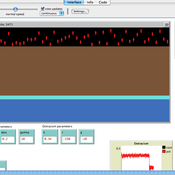
Peer reviewed FishMob: Interactions between fisher mobility and spatial resource heterogeneity
Emilie Lindkvist | Published Wednesday, October 16, 2019 | Last modified Tuesday, June 23, 2020Migration or other long-distance movement into other regions is a common strategy of fishers and fishworkers living and working on the coast to adapt to environmental change. This model attempts to understand the general dynamics of fisher mobility for over larger spatial scales. The model can be used for investigating the complex interplay that exists between mobility and fish stock heterogeneity across regions, and the associated outcomes of mobility at the system level.
The model design informed by the example of small-scale fisheries in the Gulf of California, Mexico but implements theoretical and stylized facts and can as such be used for different archetypical cases. Our methodological approach for designing the model aims to account for the complex causation, emergence and interdependencies in small-scale fisheries to explain the phenomenon of sequential overexploitation, i.e., overexploiting one resource after another. The model is intended to be used as a virtual laboratory to investigate when and how different levels of mobile fishers affect exploitation patterns of fisheries resources.
Adoption of a new regulation
Marco Janssen | Published Saturday, January 26, 2019A group of agents share a resource and agents will become sufficiently motivated to adopt a rule to constraint their freedom if they experience resource scarcity and developed mutual trust relationships.
CPNorm
Ruth Meyer | Published Sunday, June 04, 2017 | Last modified Tuesday, June 13, 2017CPNorm is a model of a community of harvesters using a common pool resource where adhering to the optimal extraction level has become a social norm. The model can be used to explore the robustness of norm-driven cooperation in the commons.
The Groundwater Commons Game
Juan Castilla-Rho Rodrigo Rojas | Published Thursday, May 11, 2017 | Last modified Saturday, September 16, 2017The Groundwater Commons Game synthesises and extends existing work on human cooperation and collective action, to elucidate possible determinants and pathways to regulatory compliance in groundwater systems globally.
This is an agent-based model that simulates the structural evolution in food supply chain.
Displaying 10 of 19 results common-pool clear search