About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 1273 results Sort by: Recently modified clear search
Zensei Wago: A Wealth-Integrated Social Capital Model
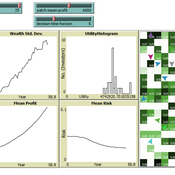
hiiki | Published Friday, May 15, 2026Interest-based compound economies generate monotonically increasing wealth inequality through multiplicative accumulation dynamics, yet the conditions under which gift-based reciprocal exchange outperforms such systems in collective well-being remain unquantified. We present Zensei Wago (全生和合), a seven-layer agent-based model comparing a Gift Resource Circulation (GRC) economy with a Compound Interest Circulation (CIC) economy under identical initial conditions. Across N = 5000 Monte Carlo replications (T = 700 ticks, N = 100 agents), GRC produced significantly higher collective resonance than CIC (p < 0.001, Cohen’s d = +0.171), above a critical prosocial threshold pm ≈ 0.698. Cohen’s d grows monotonically with duration — d = +1.943 at T = 1500 and d = +4.126 at T = 3000 — driven primarily by structural collapse of CIC resonance as inequality exceeds a critical Gini threshold (G > 0.333), while GRC resonance remains stable. The gift mechanism further decouples collective well-being from distributional outcomes, generating resonance through relational quality rather than material redistribution. Network topology analysis across seven configurations — combining a Watts-Strogatz rewiring sweep and a T = 1500 longitudinal replication — reveals that ring topology maximises GRC advantage (d = +1.17), that most topology-dependent reversals are transient (sparse and small-world both transition to significantly positive by T = 1500), and that a critical rewiring threshold of p ≈ 0.10–0.20 separates GRC-advantaged from GRC-disadvantaged network configurations. Scale-free networks remain persistently adverse (d = -7.24*), requiring structural redesign for gift-economy viability.
The Informational Assumptions of Schelling Segregation: An Agent-Based Decomposition of Cue Inference, Cultural Schemas, and Residential Sorting
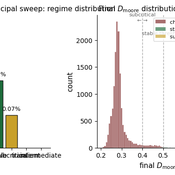
Eric Gladstone | Published Wednesday, May 13, 2026This computational model accompanies the article “The Informational Assumptions of Schelling Segregation: An Agent-Based Decomposition of Cue Inference, Cultural Schemas, and Residential Sorting.” It implements an agent-based model in which agents infer latent neighborhood-type classes from noisy non-demographic cues through schema-specific diagnostic mappings, update beliefs, and relocate when satisfaction on a preferred latent class falls below a threshold.
The model serves as a mechanism-isolation device for studying the informational architecture underlying Schelling-style residential sorting. It includes the principal sweep configuration (14,400 runs across a seven-parameter grid), a disagreement-metric sub-sweep with permutation-minimized Jensen-Shannon divergence recorded natively, controls (positive, negative, and frozen-belief), a paired-seed cue-channel perturbation experiment, and selected-cell sensitivity sweeps for cue persistence and home-biased mobility.
The full ODD protocol, parameter manifests, deterministic seed schedules, processed outputs, regenerable figure scripts, the verification test suite, and the satisfaction-mapping audit document are included. Every reported run is deterministic given a (config, seed) pair, and an included audit script verifies bit-for-bit replay on sampled runs.
Peer reviewed Integrating Reinforcement Learning in Agent-Based Modeling for Dynamic Investment Decisions
Muhammad Khurram Ali Haider Ali Hafiz Mohammad | Published Tuesday, May 05, 2026This model is a part of an ongoing research project on Multiagent Reinforcement Learning (MARL). The ODD protocol is included in the model. In this version of the model, Proximal Policy Optimization (PPO) is designed in the agent behaviors. It also includes a designed experiment in its Behavior Space which is used in the Response Surface Methodology and training of an Artificial Neural Network (ANN) based Recommender System.
Peer reviewed Flibs'NLogo - An elementary form of evolutionary cognition
Cosimo Leuci | Published Thursday, January 30, 2020Flibs’NLogo is an agent-based simulation implemented in NetLogo that models the evolution of perfect predictors through a genetic algorithm. The agents, called flibs (finite living blobs), are finite‑state automata whose behaviour is encoded in circular chromosomes. They inhabit a “primordial computer soup” and are tasked with anticipating a user‑defined periodic binary sequence. Each generation consists of 100 evaluation cycles, during which a flib’s fitness is incremented each time its output correctly matches the next environmental signal.
Reproduction follows an elitist scheme: a donor (current fittest individual) replaces a randomly chosen recipient either by cloning (complete genome substitution) or by bacterial‑like conjugation (unidirectional horizontal transfer of a random chromosome segment). A stochastic mutagenesis operator introduces point mutations in genes, while the reproductive strategy gene can also switch under a mixed-reproduction regime. Population dynamics are monitored via genomic diversity indices (Shannon‑Wiener, Simpson), a phenotypic simpleness metric that distinguishes the low number of states actually used from the genomic potential.
The model serves as a digital evolutionary laboratory for exploring the interplay among bounded rationality, collective adaptation, and the emergence of anticipatory behaviour. By linking evolutionary computation with cognitive concepts, Flibs’NLogo investigates fundamental transitions from reactive to predictive systems and allows for testing whether populations evolve toward minimal necessary complexity or exhibit an intrinsic drift toward structural elaboration.
Peer reviewed The Garbage Can Model of Organizational Choice
Guido Fioretti | Published Monday, April 20, 2020 | Last modified Thursday, April 23, 2026The Garbage Can Model of Organizational Choice is a fundamental model of organizational decision-making originally proposed by J.D. Cohen, J.G. March and J.P. Olsen in 1972. In the 2000s, G. Fioretti and A. Lomi presented a NetLogo agent-based interpretation of this model. This code is the NetLogo 6.1.1 updated version of the Fioretti-Lomi model.
Spatial Game Theory
Kristin Crouse | Published Tuesday, November 05, 2019 | Last modified Wednesday, April 22, 2026This model is a spatial evolutionary game theory model in which animals with inherited red or blue phenotypes move, interact locally, gain or lose energy based on payoff structure, and reproduce across generations. Plants provide a stationary green component of the environment. The model can be used to examine how game payoffs, inheritance, and survival shape population and evolutionary dynamics over time.
An Agent-based Model of the Tragedy of the Commons
tao liu | Published Sunday, April 12, 2026This is a model that explores how a few fishermen sharing a common fishery learn their harvesting strategies under different incentive settings, and how individual greed, cooperation, and sustainability penalties shape resource depletion and the tragedy of the commons.
Kenya ITN Agent-Based Microsimulation (2003–2024)
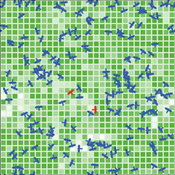
Wooyoung Kim Hosang Shin | Published Saturday, April 18, 2026An agent-based microsimulation of insecticide-treated net (ITN) distribution and adoption in Kenya (2003–2024), integrating the Theory of Planned Behaviour, Rogers diffusion, Weibull net decay, and a GPS-based two-layer social network. 8,561 household agents calibrated via Approximate Bayesian Computation to six DHS/MIS survey waves, achieving 2.42 pp mean absolute error on Kenya-level ownership. The analysis chain supports mechanism counterfactuals and policy experiments on equity outcomes of ITN distribution strategies.
The current model is designed to examine whether—and under what conditions—minority influence can generate social change. Specifically, the model assesses whether empirically validated psychological mechanisms of indirect minority influence, operating in combination, can produce system-level social change, defined as the initial minority opinion becoming the majority position. Notably, this model formalizes Moscovici’s (1976) genetic model of social influence using agent-based modeling.
Simulating Climate Stress and Social Instability: An Agent-Based Model of Ecosystem Degradation and Violence in Coastal Communities
Jacopo A. Baggio hurtado-valdivieso | Published Sunday, April 12, 2026This model is an agent-based simulation designed to explore how climate-induced environmental degradation can contribute to the emergence of social violence in coastal communities that depend heavily on ecosystem services for their livelihoods. The model represents a coupled social–ecological system in which environmental shocks—such as sea level rise and marine ecosystem decline—affect local economic conditions, food security, and community stability.
Agents in the model represent individuals whose livelihoods depend on coastal ecosystems. Environmental degradation reduces ecosystem productivity and increases economic hardship, which can lead to the formation of grievances among agents. The model incorporates behavioral thresholds that determine how individuals respond to hardship and perceived injustice. Under certain conditions—particularly when institutional capacity and law enforcement effectiveness are limited—these grievances may escalate into violent behavior.
The simulation allows users to explore how different climate scenarios, levels of ecosystem degradation, livelihood dependence, and institutional responses influence the probability of social instability and violence. By modeling the interactions between environmental stress, socio-economic vulnerability, and governance capacity, the model provides a computational framework for examining potential pathways linking climate change and conflict in coastal social–ecological systems.
…
Displaying 10 of 1273 results Sort by: Recently modified clear search