Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
Displaying 10 of 1128 results for "Bin-Tzong Chi" clear search
Can ethnic tolerance curb self-reinforcing school segregation? A theoretical Agent Based Model
Lucas Sage Andreas Flache | Published Monday, August 10, 2020Schelling and Sakoda prominently proposed computational models suggesting that strong ethnic residential segregation can be the unintended outcome of a self-reinforcing dynamic driven by choices of individuals with rather tolerant ethnic preferences. There are only few attempts to apply this view to school choice, another important arena in which ethnic segregation occurs. In the current paper, we explore with an agent-based theoretical model similar to those proposed for residential segregation, how ethnic tolerance among parents can affect the level of school segregation. More specifically, we ask whether and under which conditions school segregation could be reduced if more parents hold tolerant ethnic preferences. We move beyond earlier models of school segregation in three ways. First, we model individual school choices using a random utility discrete choice approach. Second, we vary the pattern of ethnic segregation in the residential context of school choices systematically, comparing residential maps in which segregation is unrelated to parents’ level of tolerance to residential maps reflecting their ethnic preferences. Third, we introduce heterogeneity in tolerance levels among parents belonging to the same group. Our simulation experiments suggest that ethnic school segregation can be a very robust phenomenon, occurring even when about half of the population prefers mixed to segregated schools. However, we also identify a “sweet spot” in the parameter space in which a larger proportion of tolerant parents makes the biggest difference. This is the case when parents have moderate preferences for nearby schools and there is only little residential segregation. Further experiments are presented that unravel the underlying mechanisms.
Hedonic and Eudaimonic Well-being Based Reward for Intrinsic Motivated Reinforcement Learning Agents
Yue Gao Shimon Edelman | Published Monday, March 21, 2016The code contains four experiments for well-being based IMRL reward features.
Schelling Model of the City of Salzburg
Andreas Schlagbauer | Published Monday, December 05, 2022The purpose of the model is to better understand, how different factors for human residential choices affect the city’s segregation pattern. Therefore, a Schelling (1971) model was extended to include ethnicity, income, and affordability and applied to the city of Salzburg. So far, only a few studies have tried to explore the effect of multiple factors on the residential pattern (Sahasranaman & Jensen, 2016, 2018; Yin, 2009). Thereby, models using multiple factors can produce more realistic results (Benenson et al., 2002). This model and the corresponding thesis aim to fill that gap.
Best Practices for Civic Collaboration
Wei Zhong | Published Saturday, December 20, 2008 | Last modified Saturday, April 27, 2013This is a modified version (Netlogo 4.0.3) of the model in support of Erik Johnstons dissertation, programmed in Netlogo 3.1.4 (May 15th, 2007).
Rebel Group Protection Rackets
Gerd Wagner Luis Gustavo Nardin Kamil C. Klosek Frances Duffy | Published Wednesday, December 04, 2019System Narrative
How do rebel groups control territory and engage with the local economy during civil war? Charles Tilly’s seminal War and State Making as Organized Crime (1985) posits that the process of waging war and providing governance resembles that of a protection racket, in which aspiring governing groups will extort local populations in order to gain power, and civilians or businesses will pay in order to ensure their own protection. As civil war research increasingly probes the mechanisms that fuel local disputes and the origination of violence, we develop an agent-based simulation model to explore the economic relationship of rebel groups with local populations, using extortion racket interactions to explain the dynamics of rebel fighting, their impact on the economy, and the importance of their economic base of support. This analysis provides insights for understanding the causes and byproducts of rebel competition in present-day conflicts, such as the cases of South Sudan, Afghanistan, and Somalia.
Model Description
The model defines two object types: RebelGroup and Enterprise. A RebelGroup is a group that competes for power in a system of anarchy, in which there is effectively no government control. An Enterprise is a local civilian-level actor that conducts business in this environment, whose objective is to make a profit. In this system, a RebelGroup may choose to extort money from Enterprises in order to support its fighting efforts. It can extract payments from an Enterprise, which fears for its safety if it does not pay. This adds some amount of money to the RebelGroup’s resources, and they can return to extort the same Enterprise again. The RebelGroup can also choose to loot the Enterprise instead. This results in gaining all of the Enterprise wealth, but prompts the individual Enterprise to flee, or leave the model. This reduces the available pool of Enterprises available to the RebelGroup for extortion. Following these interactions the RebelGroup can choose to AllocateWealth, or pay its rebel fighters. Depending on the value of its available resources, it can add more rebels or expel some of those which it already has, changing its size. It can also choose to expand over new territory, or effectively increase its number of potential extorting Enterprises. As a response to these dynamics, an Enterprise can choose to Report expansion to another RebelGroup, which results in fighting between the two groups. This system shows how, faced with economic choices, RebelGroups and Enterprises make decisions in war that impact conflict and violence outcomes.
Collective Decision Making for Ecological Restoration version 2.0
Dean Massey Moira Zellner Cristy Watkins Jeremy Brooks Kristen Ross Lynne M Westphal | Published Wednesday, November 19, 2014CoDMER v. 2.0 was parameterized with ethnographic data from organizations dealing with prescribed fire and seeding native plants, to advance theory on how collective decisions emerge in ecological restoration.
Network Behaviour Diffusion
Jennifer Badham | Published Saturday, October 02, 2021This model implements two types of network diffusion from an initial group of activated nodes. In complex contagion, a node is activated if the proportion of neighbour nodes that are already activated exceeds a given threshold. This is intended to represented the spread of health behaviours. In simple contagion, an activated node has a given probability of activating its inactive neighbours and re-tests each time step until all of the neighbours are activated. This is intended to represent information spread.
A range of networks are included with the model from secondary school friendship networks. The proportion of nodes initially activated and the method of selecting those nodes are controlled by the user.
Replication of the Demographic Prisoner's Dilemma
Wolfgang Radax | Published Thursday, May 02, 2013The provided source code is the result of our efforts in replicating Epstein’s Demographic Prisoner’s Dilemma. The simulation model is written in Repast/J 3.1.
RefugeePathSIM Model
Liliana Perez Saeed Harati Guillaume Arnoux Hébert | Published Thursday, October 11, 2018 | Last modified Tuesday, October 16, 2018RefugeePathSIM is an agent-based model to simulate the movement behavior of refugees in order to identify pathways of forced migration under crisis. The model generates migrants and lets them leave conflict areas for a destination that they choose based on their characteristics and desires. RefugeePathSIM has been developed and applied in a study of the Syrian war, using monthly data in years 2011-2015.
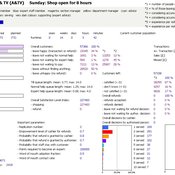
ManPraSim: A Management Practice Simulation
peer-olaf_siebers | Published Wednesday, February 23, 2011 | Last modified Saturday, April 27, 2013This simulation model is associated with the journal paper “A First Approach on Modelling Staff Proactiveness in Retail Simulation Models” to appear in the Journal of Artificial Societies and Social Simulation 14 (2) 2. The authors are Peer-Olaf Siebers ([email protected]) and Uwe Aickelin ([email protected]).
Displaying 10 of 1128 results for "Bin-Tzong Chi" clear search