About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 1273 results Sort by: Recently modified clear search
Gradient Descent Simulation
Ilyes Azouani | Published Wednesday, March 18, 2026This model visualizes gradient descent optimization - the fundamental algorithm used to train neural networks and other machine learning models. Agents represent different optimization algorithms searching for the minimum of a loss landscape (the “error surface” that ML models try to minimize during training).
The model demonstrates how different optimizer types (SGD, Momentum with different parameters) behave on various loss landscapes, from simple bowls to the notoriously difficult Rosenbrock “banana valley” function. This helps build intuition about why certain optimization algorithms work better than others for different problem geometries.
HOW IT WORKS
…
Peer reviewed The effect of homophily on co-offending outcomes
Ruslan Klymentiev Christophe Vandeviver Luis E. C. Rocha | Published Friday, September 26, 2025This Agent-Based Model is designed to simulate how similarity-based partner selection (homophily) shapes the formation of co-offending networks and the diffusion of skills within those networks. Its purpose is to isolate and test the effects of offenders’ preference for similar partners on network structure and information flow, under controlled conditions.
In the model, offenders are represented as agents with an individual attribute and a set of skills. At each time step, agents attempt to select partners based on similarity preference. When two agents mutually select each other, they commit a co-offense, forming a tie and exchanging a skill. The model tracks the evolution of network properties (e.g., density, clustering, and tie strength) as well as the spread of skills over time.
This simple and theoretical model does not aim to produce precise empirical predictions but rather to generate insights and test hypotheses about the trade-off between partnership stability and information diffusion. It provides a flexible framework for exploring how changes in partner selection preferences may lead to differences in criminal network dynamics. Although the model was developed to simulate offenders’ interactions, in principle, it could be applied to other social processes involving social learning and skills exchange.
…
NetLogo Model of Spatial Eviction in Attraction-Repulsion Opinion Dynamics
poyeker | Published Friday, March 13, 2026A reproducible NetLogo implementation of a spatial attraction-repulsion opinion model with eviction-driven relocation. Agents interact locally, converge with similar neighbors, diverge from dissimilar neighbors, and may evict the most dissimilar neighbor to a random empty location. Parameter sweeps reveal transitions among extremist, mixed, and consensus regimes, with outputs including phase diagrams, opinion distributions, and Moran’s I. The model is intended to reproduce and extend results on how exclusion frequency changes polarization outcomes.
Exploring the aftermath of transition failures: An agent-based model
Gangmin Park Junmin Lee Jisoo Lee Keungoui Kim | Published Friday, March 06, 2026This computational model is an agent-based model (ABM) developed to investigate how repeated failures of emerging niches accumulate and influence the trajectory of socio-technical transitions. Built in AnyLogic 8.7.11, the model simulates the dynamic interactions between a dominant regime and sequential niche entrants within a two-dimensional practice space. It models alignment, movement, and competition based on technological maturity and market penetration. The model utilizes a reinforcing feedback structure linking consumer support, output, resource accumulation, and capacity development (Physical and Institutional Capacity). A complete model specification following the ODD+D (Overview, Design concepts, Details, and Decision) protocol is included in the documentation.
Peer reviewed MADTOR: Model for Assessing Drug Trafficking Organizations Resilience
Deborah Manzi | Published Friday, February 23, 2024 | Last modified Friday, February 27, 2026Criminal organizations operate in complex changing environments. Being flexible and dynamic allows criminal networks not only to exploit new illicit opportunities but also to react to law enforcement attempts at disruption, enhancing the persistence of these networks over time. Most studies investigating network disruption have examined organizational structures before and after the arrests of some actors but have disregarded groups’ adaptation strategies.
MADTOR simulates drug trafficking and dealing activities by organized criminal groups and their reactions to law enforcement attempts at disruption. The simulation relied on information retrieved from a detailed court order against a large-scale Italian drug trafficking organization (DTO) and from the literature.
The results showed that the higher the proportion of members arrested, the greater the challenges for DTOs, with higher rates of disrupted organizations and long-term consequences for surviving DTOs. Second, targeting members performing specific tasks had different impacts on DTO resilience: targeting traffickers resulted in the highest rates of DTO disruption, while targeting actors in charge of more redundant tasks (e.g., retailers) had smaller but significant impacts. Third, the model examined the resistance and resilience of DTOs adopting different strategies in the security/efficiency trade-off. Efficient DTOs were more resilient, outperforming secure DTOs in terms of reactions to a single, equal attempt at disruption. Conversely, secure DTOs were more resistant, displaying higher survival rates than efficient DTOs when considering the differentiated frequency and effectiveness of law enforcement interventions on DTOs having different focuses in the security/efficiency trade-off.
Overall, the model demonstrated that law enforcement interventions are often critical events for DTOs, with high rates of both first intention (i.e., DTOs directly disrupted by the intervention) and second intention (i.e., DTOs terminating their activities due to the unsustainability of the intervention’s short-term consequences) culminating in dismantlement. However, surviving DTOs always displayed a high level of resilience, with effective strategies in place to react to threatening events and to continue drug trafficking and dealing.
Peer reviewed A dynamic identity model for misinformation in social networks
emdhar | Published Friday, February 27, 2026A dynamic identity model for misinformation in social networks, an agent-based model of social identity and misinformation dynamics.
I developed this model as a part of my master’s thesis, “Does social identity drive belief and persistence in online misinformation? An agent-based modelling approach” at University College Dublin, Ireland (2024-2025).
The purpose of this model is to further understand the dynamics of misinformation sharing as an expression of social identity. I introduce a framework to understand the influence of self-categorisation on misinformation persistence in social network. It integrates a social learning model with the Dynamic Identity Model for Agents (DIMA) using simple logic to simulate the social trade-offs driving misinformation and observe the effects on misinformation spread.
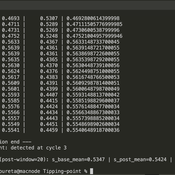
Peer reviewed Green Consumption Tipping Point
Mario | Published Thursday, February 26, 2026This model is a minimal agent-based model (ABM) of green consumption and market tipping dynamics in a stylised two-firm economy. It is designed as an existence proof to illustrate how weak individual preferences, when combined with habit formation, social influence, and firm price adaptation, can generate non-linear transitions (tipping points) in market outcomes.
The economy consists of:
1) Two firms, each supplying a differentiated consumption bundle that differs in its fixed green share (one relatively greener, one less green).
2) Many households, each consuming a unit mass per period and allocating consumption between the two firms.
…
Peer reviewed Evolution of Sex
Kristin Crouse | Published Sunday, June 05, 2016 | Last modified Wednesday, February 18, 2026Evolution of Sex is a NetLogo model that illustrates the advantages and disadvantages of sexual and asexual reproductive strategies. It seeks to demonstrate the answer to the question “Why do we have sex?”
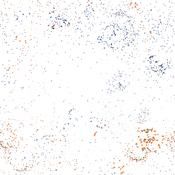
Selective Depolarization by Endogenous Migration in Attraction-Repulsion Opinion Dynamics (NetLogo)
poyeker | Published Tuesday, February 17, 2026This model implements a coupled opinion-mobility agent-based framework in NetLogo, extending Attraction-Repulsion Model (ARM) dynamics with endogenous migration in continuous 2D space.
Each agent has an opinion s in [0,1] and a spatial position (x,y). Agents interact locally within an interaction radius, with exposure-controlled interaction probability. Opinion updates follow ARM rules: attraction for small opinion distance and repulsion for large distance (tolerance threshold T). After social interaction, agents move according to a social-force mechanism that balances attraction to similar neighbors and avoidance of dissimilar neighbors, controlled by orientation bias (approaching goods vs leaving bads). The model also includes an optional exposure-mobility coupling setting.
Main outputs include polarization (P), spatial assortativity (Moran’s I), mixed-neighbor fraction (f_mix), and good-component count (N_g). The model is designed to study phase behavior of polarization and segregation under mobility and tolerance heterogeneity.
…
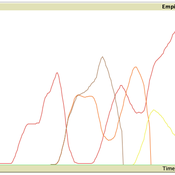
Replica of Turchin's (2003) Metaethnic Frontier model
Paul Smaldino | Published Sunday, February 15, 2026In his 2003 book, Historical Dynamics (ch. 4), Turchin describes and briefly analyzes a spatial ABM of his metaethnic frontier theory, which is essentially a formalization of a theory by Ibn Khaldun in the 14th century. In the model, polities compete with neighboring polities and can absorb them into an empire. Groups possess “asabiya”, a measure of social solidarity and a sense of shared purpose. Regions that share borders with other groups will have increased asabiya do to salient us vs. them competition. High asabiya enhances the ability to grow, work together, and hence wage war on neighboring groups and assimilate them into an empire. The larger the frontier, the higher the empire’s asabiya.
As an empire expands, (1) increased access to resources drives further growth; (2) internal conflict decreases asabiya among those who live far from the frontier; and (3) expanded size of the frontier decreases ability to wage war along all frontiers. When an empire’s asabiya decreases too much, it collapses. Another group with more compelling asabiya eventually helps establish a new empire.
Displaying 10 of 1273 results Sort by: Recently modified clear search