About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 14 results team performance clear search
Autonomy or control? An agent-based study of self-organising versus centralised task allocation
Shaoni Wang | Published Wednesday, January 29, 2025The aim of our model is to investigate the team dynamics through two types of task allocation strategies, with a focus on the dynamic interplay between individual needs and group performance. To achieve this goal, we have formulated an agent-based model (ABM) to formalize Deci & Ryan’s self-determination theory (SDT) and explore the social dynamics that govern the relationship between individual and group levels of team performance.
Team Structure and Task Performance
Davide Secchi Martin Neumann | Published Monday, August 05, 2024This model was designed to study resilience in organizations. Inspired by ethnographic work, it follows the simple goal to understand whether team structure affects the way in which tasks are performed. In so doing, it compares the ‘hybrid’ data-inspired structure with three more traditional structures (i.e. hierarchy, flexible/relaxed hierarchy, and anarchy/disorganization).
The influence of cognitive diversity on networked search and coordination
César García-Díaz | Published Wednesday, April 03, 2024Agent-based models of organizational search have long investigated how exploitative and exploratory behaviors shape and affect performance on complex landscapes. To explore this further, we build a series of models where agents have different levels of expertise and cognitive capabilities, so they must rely on each other’s knowledge to navigate the landscape. Model A investigates performance results for efficient and inefficient networks. Building on Model B, it adds individual-level cognitive diversity and interaction based on knowledge similarity. Model C then explores the performance implications of coordination spaces. Results show that totally connected networks outperform both hierarchical and clustered network structures when there are clear signals to detect neighbor performance. However, this pattern is reversed when agents must rely on experiential search and follow a path-dependent exploration pattern.
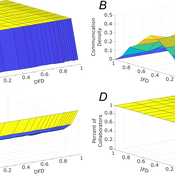
Role of Diversity in Team Performance: the Case of Missing Expertise, an Agent Based Simulations
Tamás Kiss | Published Friday, December 29, 2023This ABM simulates problem solving agents as they work on a set of tasks. Each agent has a trait vector describing their skills. Two agents might form a collaboration if their traits are similar enough. Tasks are defined by a component vector. Agents work on tasks by decreasing tasks’ component vectors towards zero.
The simulation generates agents with given intrapersonal functional diversity (IFD), and dominant function diversity (DFD), and a set of random tasks and evaluates how agents’ traits influence their level of communication and the performance of a team of agents.
Modeling results highlight the importance of the distributions of agents’ properties forming a team, and suggests that for a thorough description of management teams, not only diversity measures based on individual agents, but an aggregate measure is also required.
…
Peer reviewed A Computational Simulation for Task Allocation Influencing Performance in the Team System
Shaoni Wang | Published Friday, November 11, 2022 | Last modified Thursday, April 06, 2023This model system aims to simulate the whole process of task allocation, task execution and evaluation in the team system through a feasible method. On the basis of Complex Adaptive Systems (CAS) theory and Agent-based Modelling (ABM) technologies and tools, this simulation system attempts to abstract real-world teams into MAS models. The author designs various task allocation strategies according to different perspectives, and the interaction among members is concerned during the task-performing process. Additionally, knowledge can be acquired by such an interaction process if members encounter tasks they cannot handle directly. An artificial computational team is constructed through ABM in this simulation system, to replace real teams and carry out computational experiments. In all, this model system has great potential for studying team dynamics, and model explorers are encouraged to expand on this to develop richer models for research.
Superiority Bias and Communication Noise in a Model of Collective Problem Solving
Paul Smaldino Amin Boroomand | Published Sunday, May 01, 2022This model aims to examine how different levels of communication noise and superiority bias affect team performance when solving problems collectively. We used a networked agent-based model of collective problem solving in which agents explore the NK landscape for a better solution and communicate with each other regarding their current solutions. We compared the team performance in solving problems collectively at different levels of self-superiority bias when facing simple and complex problems. Additionally, we addressed the effect of different levels of communication noise on the team’s outcome
Peer reviewed The dynamical relationship between individual needs and group performance: A simulation of the self-organising task allocation process
Shaoni Wang | Published Tuesday, October 05, 2021The purpose of the model is to study the dynamical relationship between individual needs and group performance when focusing on self-organizing task allocation. For this, we develop a model that formalizes Deci & Ryan’s self-determination theory (SDT) theory into an ABM creating a framework to study the social dynamics that pertain to the mutual relations between the individual and group level of team performance. Specifically, it aims to answer how the three individual motivations of autonomy, competence, and belonging affect team performance.
Knowledge Based Economy
Guido Fioretti Sirio Capizzi Ruggero Rossi Martina Casari Ala Jlif | Published Tuesday, May 18, 2021Knowledge Based Economy (KBE) is an artificial economy where firms placed in geographical space develop original knowledge, imitate one another and eventually recombine pieces of knowledge. In KBE, consumer value arises from the capability of certain pieces of knowledge to bridge between existing items (e.g., Steve Jobs illustrated the first smartphone explaining that you could make a call with it, but also listen to music and navigate the Internet). Since KBE includes a mechanism for the generation of value, it works without utility functions and does not need to model market exchanges.
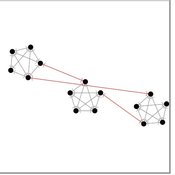
The Effect of Individual and Collective Characteristics on Team Performance: A Model of Networked Agents Engaged in Collective Problem Solving
Amin Boroomand | Published Tuesday, March 16, 2021 | Last modified Monday, July 26, 2021This code is for an agent-based model of collective problem solving in which agents with different behavior strategies, explore the NK landscape while they communicate with their peers agents. This model is based on the famous work of Lazer, D., & Friedman, A. (2007), The network structure of exploration and exploitation.
The uFUNK Model
Davide Secchi | Published Monday, August 31, 2020The agent-based simulation is set to work on information that is either (a) functional, (b) pseudo-functional, (c) dysfunctional, or (d) irrelevant. The idea is that a judgment on whether information falls into one of the four categories is based on the agent and its network. In other words, it is the agents who interprets a particular information as being (a), (b), (c), or (d). It is a decision based on an exchange with co-workers. This makes the judgment a socially-grounded cognitive exercise. The uFUNK 1.0.2 Model is set on an organization where agent-employee work on agent-tasks.
Displaying 10 of 14 results team performance clear search