About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 361 results for "John C Moore" clear search
Exploring organizational learning in innovation networks. An agent-based model
Sandra Schmid | Published Saturday, March 07, 2015This agent-based model represents a stylized inter-organizational innovation network where firms collaborate with each other in order to generate novel organizational knowledge.
Health and social public information office (SPUN) simulation
Emilio Sulis Manuela Vinai | Published Friday, November 06, 2015 | Last modified Saturday, November 07, 2015The program simulate the functioning of an italian health and social public information office (SPUN) on the basis of the real data collected in the first five years of functioning.
HomininSpace
Fulco Scherjon | Published Friday, November 25, 2016 | Last modified Tuesday, October 06, 2020A modelling system to simulate Neanderthal demography and distribution in a reconstructed Western Europe for the late Middle Paleolithic.
Climate Change Adaptation in Coastal Regions
Emma Cutler | Published Thursday, June 01, 2017This generic model simulates climate change adaptation in the form of resistance, accommodation, and retreat in coastal regions vulnerable to sea level rise and flooding. It tracks how population changes as households retreat to higher ground.
The Evolution of Multiple Resistant Strains: An Abstract Model of Systemic Treatment and Accumulated Resistance
Benjamin Nye | Published Wednesday, August 31, 2011 | Last modified Saturday, April 27, 2013This model is intended to explore the effectiveness of different courses of interventions on an abstract population of infections. Illustrative findings highlight the importance of the mechanisms for variability and mutation on the effectiveness of different interventions.
Peer reviewed Minding Norms in an Epidemic Does Matter
Klaus G. Troitzsch | Published Saturday, February 27, 2021 | Last modified Monday, September 13, 2021This paper tries to shed some light on the mutual influence of citizen behaviour and the spread of a virus in an epidemic. While the spread of a virus from infectious to susceptible persons and the outbreak of an infection leading to more or less severe illness and, finally, to recovery and immunity or death has been modelled with different kinds of models in the past, the influence of certain behaviours to keep the epidemic low and to follow recommendations of others to apply these behaviours has rarely been modelled. The model introduced here uses a theory of the effect of norm invocations among persons to find out the effect of spreading norms interacts with the progress of an epidemic. Results show that norm invocations matter. The model replicates the histories of the COVID-19 epidemic in various region, including “second waves” (but only until the end of 2021 as afterwards the official statistics ceased to be reliable as many infected persons did not report their positive test results after countermeasures were relieved), and shows that the calculation of the reproduction numbers from current reported infections usually overestimates the “real” but in practice unobservable reproduction number.
How information propagation in hybrid spaces affects decision-making: using ABM to simulate Covid-19 vaccine uptake
Fuzhen Yin | Published Wednesday, March 13, 2024Abstract: The notion of physical space has long been central in geographical theories. However, the widespread adoption of information and communication technologies (ICTs) has freed human dynamics from purely physical to also relational and cyber spaces. While researchers increasingly recognize such shifts, rarely have studies examined how the information propagates in these hybrid spaces (i.e., physical, relational, and cyber). By exploring the vaccine opinion dynamics through agent-based modeling, this study is the first that combines all hybrid spaces and explores their distinct impacts on human dynamics from an individual’s perspective. Our model captures the temporal dynamics of vaccination progress with small errors (MAE=2.45). Our results suggest that all hybrid spaces are indispensable in vaccination decision making. However, in our model, most of the agents tend to give more emphasis to the information that is spread in the physical instead of other hybrid spaces. Our study not only sheds light on human dynamics research but also offers a new lens to identifying vaccinated individuals which has long been challenging in disease-spread models. Furthermore, our study also provides responses for practitioners to develop vaccination outreach policies and plan for future outbreaks.
Peer reviewed Urban Transport Mode Choices
Kathleen Salazar -Serna Lorena Cadavid Carlos Franco | Published Thursday, May 22, 2025The model represents urban commuters’ transport mode choices among cars, public transit, and motorcycles—a mode highly prevalent in developing countries. Using an agent-based modeling approach, it simulates transport dynamics and serves as a testbed for evaluating policies aimed at improving mobility.
The model simulates an ecosystem of human agents who decide, at each time step, which mode of transportation to use for commuting to work. Their decision is based on a combination of personal satisfaction with their most recent journey—evaluated across a vector of individual needs—the information they crowdsource from their social network, and their personal uncertainty regarding trying new transport options.
Agents are assigned demographic attributes such as sex, age, and income level, and are distributed across city neighborhoods according to their socioeconomic status. To represent social influence in decision-making, agents are connected via a scale-free social network topology, where connections are more likely among agents within the same socioeconomic group, reflecting the tendency of individuals to form social ties with similar others.
…
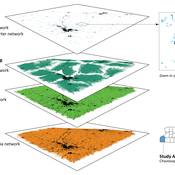
An empirical ABM for regional land use/cover change: a Dutch case study
Diego Valbuena | Published Saturday, March 12, 2011 | Last modified Thursday, November 11, 2021This is an empirical model described in http://dx.doi.org/10.1016/j.landurbplan.2010.05.001. The objective of the model is to simulate how the decision-making of farmers/agents with different strategies can affect the landscape structure in a region in the Netherlands.
Peer reviewed Torsten Hägerstrand’s Spatial Innovation Diffusion Model
Sean Bergin | Published Friday, September 14, 2012 | Last modified Saturday, April 27, 2013This model is a replication of Torsten Hägerstrand’s 1965 model–one of the earliest known calibrated and validated simulations with implicit “agent based” methodology.
Displaying 10 of 361 results for "John C Moore" clear search