About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 989 results for "Dave van Wees" clear search
Emission Trading Impact On Power Generation Model
Emile Chappin | Published Friday, June 19, 2020Under the Kyoto Protocol, governments agreed on and accepted CO2 reduction targets in order to counter climate change. In Europe one of the main policy instruments to meet the agreed reduction targets is CO2 emission-trading (CET), which was implemented as of January 2005. In this system, companies active in specific sectors must be in the possession of CO2 emission rights to an amount equal to their CO2 emission. In Europe, electricity generation accounts for one-third of CO2 emissions. Since the power generation sector, has been liberalized, reregulated and privatized in the last decade, around Europe autonomous companies determine the sectors’ CO2 emission. Short-term they adjust their operation, long-term they decide on (dis)investment in power generation facilities and technology selection. An agent-based model is presented to elucidate the effect of CET on the decisions of power companies in an oligopolistic market. Simulations over an extensive scenario-space show that there CET does have an impact. A long-term portfolio shift towards less-CO2 intensive power generation is observed. However, the effect of CET is relatively small and materializes late. The absolute emissions from power generation rise under most scenarios. This corresponds to the dominant character of current capacity expansion planned in the Netherlands (50%) and in Germany (68%), where companies have announced many new coal based power plants. Coal is the most CO2 intensive option available and it seems surprising that even after the introduction of CET these capacity expansion plans indicate a preference for coal. Apparently in power generation the economic effect of CO2 emission-trading is not sufficient to outweigh the economic incentives to choose for coal.
The Thin Blue Line Between Protesters and Their Counter-Protesters
Tamsin Lee | Published Monday, March 26, 2018More frequently protests are accompanied by an opposing group performing a counter protest. This phenomenon can increase tension such that police must try to keep the two groups separated. However, what is the best strategy for police? This paper uses a simple agent-based model to determine the best strategy for keeping the two groups separated. The ‘thin blue line’ varies in density (number of police), width and the keenness of police to approach protesters. Three different groups of protesters are modelled to mimic peaceful, average and volatile protests. In most cases, a few police forming a single-file ‘thin blue line’ separating the groups is very effective. However, when the protests are more volatile, it is more effective to have many police occupying a wide ‘thin blue line’, and police being keen to approach protesters. To the authors knowledge, this is the first paper to model protests and counter-protests.
ICARUS - a multi-agent compliance inspection model
Slaven Smojver | Published Monday, May 09, 2022ICARUS is a multi-agent compliance inspection model (ICARUS - Inspecting Compliance to mAny RUleS). The model is applicable to environments where an inspection agency, via centrally coordinated inspections, examines compliance in organizations which must comply with multiple provisions (rules). The model (ICARUS) contains 3 types of agents: entities, inspection agency and inspectors / inspections. ICARUS describes a repeated, simultaneous, non-cooperative game of pure competition. Agents have imperfect, incomplete, asymmetric information. Entities in each move (tick) choose a pure strategy (comply/violate) for each rule, depending on their own subjective assessment of the probability of the inspection. The Inspection Agency carries out the given inspection strategy.
A more detailed description of the model is available in the .nlogo file.
Full description of the model (in line with the ODD+D protocol) and the analysis of the model (including verification, validation and sensitivity analysis) can be found in the attached documentation.
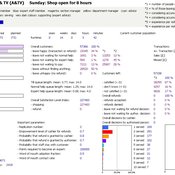
ManPraSim: A Management Practice Simulation
peer-olaf_siebers | Published Wednesday, February 23, 2011 | Last modified Saturday, April 27, 2013This simulation model is associated with the journal paper “A First Approach on Modelling Staff Proactiveness in Retail Simulation Models” to appear in the Journal of Artificial Societies and Social Simulation 14 (2) 2. The authors are Peer-Olaf Siebers ([email protected]) and Uwe Aickelin ([email protected]).
Investor-based electricity market model
Oscar Kraan | Published Monday, January 02, 2017 | Last modified Friday, October 12, 2018The model is a representation of a liberalised electricity market designed as an energy-only market and consists of large scale investors and their power generation assets in the electricity market.
Wildlife-Human Interactions in Shared Landscapes (WHISL)
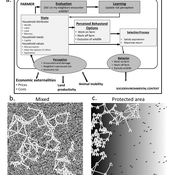
Nicholas Magliocca Neil Carter Andres Baeza-Castro | Published Friday, May 22, 2020This model simulates a group of farmers that have encounters with individuals of a wildlife population. Each farmer owns a set of cells that represent their farm. Each farmer must decide what cells inside their farm will be used to produce an agricultural good that is self in an external market at a given price. The farmer must decide to protect the farm from potential encounters with individuals of the wildlife population. This decision in the model is called “fencing”. Each time that a cell is fenced, the chances of a wildlife individual to move to that cell is reduced. Each encounter reduces the productive outcome obtained of the affected cell. Farmers, therefore, can reduce the risk of encounters by exclusion. The decision of excluding wildlife is made considering the perception of risk of encounters. In the model, the perception of risk is subjective, as it depends on past encounters and on the perception of risk from other farmers in the community. The community of farmers passes information about this risk perception through a social network. The user (observer) of the model can control the importance of the social network on the individual perception of risk.
Income and Expenditure
Tony Lawson | Published Thursday, October 06, 2011 | Last modified Saturday, April 27, 2013How do households alter their spending patterns when they experience changes in income? This model answers this question using a random assignment scheme where spending patterns are copied from a household in the new income bracket.
Hybrid agent-based methodology for testing response protocols
Fernando Sancho Caparrini | Published Wednesday, February 03, 2021In recent years we have seen multiple incidents with a large number of people injured and killed by one or more armed attackers. Since this type of violence is difficult to predict, detecting threats as early as possible allows to generate early warnings and reduce response time. In this context, any tool to check and compare different action protocols can be a further step in the direction of saving lives. Our proposal combines features from continuous and discrete models to obtain the best of both worlds in order to simulate large and crowded spaces where complex behavior individuals interact. With this proposal we aim to provide a tool for testing different security protocols under several emergency scenarios, where spaces, hazards, and population can be customized. Finally, we use a proof of concept implementation of this model to test specific security protocols under emergency situations for real spaces. Specifically, we test how providing some users of a university college with an app that informs about the type and characteristics of the ongoing hazard, affects in the safety performance.
Using Agent-Based Modelling and Reinforcement Learning to Study Hybrid Threats
kpadur | Published Friday, September 20, 2024Hybrid attacks coordinate the exploitation of vulnerabilities across domains to undermine trust in authorities and cause social unrest. Whilst such attacks have primarily been seen in active conflict zones, there is growing concern about the potential harm that can be caused by hybrid attacks more generally and a desire to discover how better to identify and react to them. In addressing such threats, it is important to be able to identify and understand an adversary’s behaviour. Game theory is the approach predominantly used in security and defence literature for this purpose. However, the underlying rationality assumption, the equilibrium concept of game theory, as well as the need to make simplifying assumptions can limit its use in the study of emerging threats. To study hybrid threats, we present a novel agent-based model in which, for the first time, agents use reinforcement learning to inform their decisions. This model allows us to investigate the behavioural strategies of threat agents with hybrid attack capabilities as well as their broader impact on the behaviours and opinions of other agents.
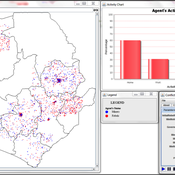
The Geography of Conflict Diamonds: The Case of Sierra Leone
Andrew Crooks Bianica Pires | Published Thursday, March 24, 2016 | Last modified Thursday, March 24, 2016Using Sierra Leone as a test case, the purpose of the model is to explore the role of geography in a resource-driven war. An ABM is integrated with geographic information systems (GIS) for this purpose.
Displaying 10 of 989 results for "Dave van Wees" clear search