Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
Displaying 10 of 1142 results for "Sjoukje A Osinga" clear search
Peer reviewed Charging behaviour of electric vehicle drivers
Wilfried van Sark Annemijn Peters Floor Alkemade Mart van der Kam | Published Wednesday, May 08, 2019 | Last modified Tuesday, April 14, 2020This model was developed to study the combination of electric vehicles (EVs) and intermitten renewable energy sources. The model presents an EV fleet in a fictional area, divided into a residential area, an office area and commercial area. The area has renewable energy sources: wind and PV solar panels. The agents can be encouraged to charge their electric vehicles at times of renewable energy surplus by introducing different policy interventions. Other interesting variables in the model are the installed renewable energy sources, EV fleet composition and available charging infrastructure. Where possible, use emperical data as input for our model. We expand upon previous models by incorporating environmental self-identity and range anxiety as agent variables.
The Internal Organizational Plasticity Model (IOP 2.1.2)
Davide Secchi | Published Tuesday, June 02, 2020IOP 2.1.2 is an agent-based simulation model designed to explore the relations between (1) employees, (2) tasks and (3) resources in an organizational setting. By comparing alternative cognitive strategies in the use of resources, employees face increasingly demanding waves of tasks that derive by challenges the organization face to adapt to a turbulent environment. The assumption tested by this model is that a successful organizational adaptation, called plastic, is necessarily tied to how employees handle pressure coming from existing and new tasks. By comparing alternative cognitive strategies, connected to ‘docility’ (Simon, 1993; Secchi, 2011) and ‘extended’ cognition (Clark, 2003, Secchi & Cowley, 2018), IOP 2.1.2 is an attempt to indicate which strategy is most suitable and under which scenario.
University Connectivity
Rachel Wozniak Nick Glover Chris English Juan Cisneros | Published Tuesday, November 30, 2021This model is designed to show the effects of personality types and student organizations have on ones chance to making friendships in a university setting. As known from psychology studies, those that are extroverted have an easier chance making friendships in comparison to those that are introverted.
Once every tick a pair of students (nodes) will be randomly selected they will then have the chance to either be come friends or not (create an edge or not) based on their personality type (you are able to change what the effect of each personality is) and whether or not they are in the same club (you can change this value) then the model triggers the next tick cycle to begin.
Protein 2.0: An Agent-Based Model for Simulating Norway’s Protein Sector Under Carbon Pricing and the Emergence of Cultivated Proteins
Gary Polhill Nick Roxburgh Rob J.F. Burton Klaus Mittenzwei | Published Thursday, May 08, 2025Protein 2.0 is a systems model of the Norwegian protein sector designed to explore the potential impacts of carbon taxation and the emergence of cultivated meat and dairy technologies. The model simulates production, pricing, and consumption dynamics across conventional and cultivated protein sources, accounting for emissions intensity, technological learning, economies of scale, and agent behaviour. It assesses how carbon pricing could alter the competitiveness of conventional beef, lamb, pork, chicken, milk, and egg production relative to emerging cultivated alternatives, and evaluates the implications for domestic production, emissions, and food system resilience. The model provides a flexible platform for exploring policy scenarios and transition pathways in protein supply. Further details can be found in the associated publication.
Aquarium
Yunshuo Tang | Published Tuesday, May 26, 2026This model simulates a simple aquatic ecosystem containing fish and food. It explores how individual interactions such as movement, feeding, and reproduction shape the population dynamics of fish over time.
Effective population size and cultural evolution
Luke Premo | Published Tuesday, May 17, 2016This model illustrates how the effective population size and the rate of change in mean skill level of a cultural trait are affected by the presence of natural selection and/or the cultural transmission mechanism by which it is passed.
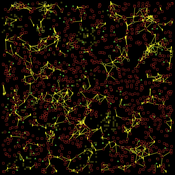
PA/C model with affinity
N. Leticia Abrica-Jacinto Evguenii Kurmyshev Héctor Juárez | Published Thursday, October 27, 2016We expose RA agent-based model of the opinion and tolerance dynamics in artificial societies. The formal mathematical model is based on the ideas of Social Influence, Social Judgment, and Social Identity theories.
NetLogo-R-Example for the Inititialisation of Agents with Correlated Random Numbers
Danilo Saft | Published Friday, February 14, 2014 | Last modified Monday, April 08, 2019This is a short NetLogo example demonstrating how to initialize 500 agents with 4 correlated parameters each with random values by doing the necessary calculations in the program “R” and retrieving the results.
Metaphoria 2019 eternal mutation
Timothy Gooding | Published Sunday, February 24, 2019This model is a modification of Metaphoria 2019, where the monetary system can be run with agents that do not die, but their characteristics are mutated as they are in the mortal population.
Evaluating Government's Policies on Promoting Smart Metering Diffusion in Retail Electricity Markets
Tao Zhang | Published Monday, December 07, 2009 | Last modified Saturday, April 27, 2013This model is a market game for evaluating the effectiveness of the UK government’s 2008-2010 policy on promoting smart metering in the UK retail electricity market. We break down the policy into four
Displaying 10 of 1142 results for "Sjoukje A Osinga" clear search