About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 121 results decision making clear search
BESTMAP-ABM-DE is an agent-based model to determine the adoption and spatial allocation of selected agri-environmental schemes (AES) by individual farmers in the Mulde River Basin located in Western Saxony, Germany. The selected AES are buffer areas, cover crops, maintaining permanent grassland and conversion of arable land to permanent grassland. While the first three schemes have already been offered in the case study area, the latter scheme is a hypothetical scheme designed to test the impact of potential policy changes. For the first model analyses, only the currently offered schemes are considered. With the model, the effect of different scenarios of policy design on patterns of adoption can be investigated. In particular, the model can be used to study the social-ecological consequences of agricultural policies at different spatial and temporal scales and, in combination with biophysical models, test the ecological implications of different designs of the EU’s Common Agricultural Policy. The model was developed in the BESTMAP project.
Peer reviewed soslivestock model
Marco Janssen Irene Perez Ibarra Diego J. Soler-Navarro Alicia Tenza Peral | Published Wednesday, May 28, 2025 | Last modified Tuesday, June 10, 2025The purpose of this model is to analyze how different management strategies affect the wellbeing, sustainability and resilience of an extensive livestock system under scenarios of climate change and landscape configurations. For this purpose, it simulates one cattle farming system, in which agents (cattle) move through the space using resources (grass). Three farmer profiles are considered: 1) a subsistence farmer that emphasizes self-sufficiency and low costs with limited attention to herd management practices, 2) a commercial farmer focused on profit maximization through efficient production methods, and 3) an environmental farmer that prioritizes conservation of natural resources and animal welfare over profit maximization. These three farmer profiles share the same management strategies to adapt to climate and resource conditions, but differ in their goals and decision-making criteria for when, how, and whether to implement those strategies. This model is based on the SequiaBasalto model (Dieguez Cameroni et al. 2012, 2014, Bommel et al. 2014 and Morales et al. 2015), replicated in NetLogo by Soler-Navarro et al. (2023).
One year is 368 days. Seasons change every 92 days. Each step begins with the growth of grass as a function of climate and season. This is followed by updating the live weight of animals according to the grass height of their patch, and grass consumption, which is determined based on the updated live weight. Animals can be supplemented by the farmer in case of severe drought. After consumption, cows grow and reproduce, and a new grass height is calculated. This updated grass height value becomes the starting grass height for the next day. Cows then move to the next area with the highest grass height. After that, cattle prices are updated and cattle sales are held on the first day of fall. In the event of a severe drought, special sales are held. Finally, at the end of the day, the farm balance and the farmer’s effort are calculated.
Peer reviewed Urban Transport Mode Choices
Kathleen Salazar -Serna Lorena Cadavid Carlos Franco | Published Thursday, May 22, 2025The model represents urban commuters’ transport mode choices among cars, public transit, and motorcycles—a mode highly prevalent in developing countries. Using an agent-based modeling approach, it simulates transport dynamics and serves as a testbed for evaluating policies aimed at improving mobility.
The model simulates an ecosystem of human agents who decide, at each time step, which mode of transportation to use for commuting to work. Their decision is based on a combination of personal satisfaction with their most recent journey—evaluated across a vector of individual needs—the information they crowdsource from their social network, and their personal uncertainty regarding trying new transport options.
Agents are assigned demographic attributes such as sex, age, and income level, and are distributed across city neighborhoods according to their socioeconomic status. To represent social influence in decision-making, agents are connected via a scale-free social network topology, where connections are more likely among agents within the same socioeconomic group, reflecting the tendency of individuals to form social ties with similar others.
…
Agent-Based Model for Multiple Team Membership (ABMMTM)
Andrew Collins | Published Thursday, April 03, 2025The Agent-Based Model for Multiple Team Membership (ABMMTM) simulates design teams searching for viable design solutions, for a large design project that requires multiple design teams that are working simultaneously, under different organizational structures; specifically, the impact of multiple team membership (MTM). The key mechanism under study is how individual agent-level decision-making impacts macro-level project performance, specifically, wage cost. Each agent follows a stochastic learning approach, akin to simulated annealing or reinforcement learning, where they iteratively explore potential design solutions. The agent evaluates new solutions based on a random-walk exploration, accepting improvements while rejecting inferior designs. This iterative process simulates real-world problem-solving dynamics where designers refine solutions based on feedback.
As a proof-of-concept demonstration of assessing the macro-level effects of MTM in organizational design, we developed this agent-based simulation model which was used in a simulation experiment. The scenario is a system design project involving multiple interdependent teams of engineering designers. In this scenario, the required system design is split into three separate but interdependent systems, e.g., the design of a satellite could (trivially) be split into three components: power source, control system, and communication systems; each of three design team is in charge of a design of one of these components. A design team is responsible for ensuring its proposed component’s design meets the design requirement; they are not responsible for the design requirements of the other components. If the design of a given component does not affect the design requirements of the other components, we call this the uncoupled scenario; otherwise, it is a coupled scenario.
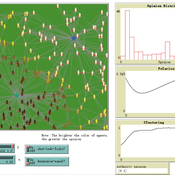
How Does Culture Affect Vaccination Opinion Polarisation?
Teng Li | Published Monday, March 10, 2025This model is to explore how individuals’ cultural backgrounds may play a role in their Covid vaccination decision-making. Two cultural dimensions of collectivism/individualism and power distance are considered. Through the experimental scenarios, we find that Covid-vaccination opinions in collectivist societies can also be considerably polarised, if the power distance is less and authorities less centralised. This result complements the popular idea that cultural collectivism is usually associated with a high degree of social consensus. Hopefully, this study will help explain countries’ difference in the response of Covid vaccination programs.
Timing and certainty in evidence-based decision-making
Sacha Ferrari | Published Saturday, January 25, 2025Model implemented in Lammers, W., Pattyn, V., Ferrari, S. et al. Evidence for policy-makers: A matter of timing and certainty?. Policy Sci 57, 171–191 (2024). https://doi.org/10.1007/s11077-024-09526-9
Soy2Grow-ABM-V1
Siavash Farahbakhsh | Published Monday, January 20, 2025The Soy2Grow ABM aims to simulate the adoption of soybean production in Flanders, Belgium. The model primarily considers two types of agents as farmers: 1) arable and 2) dairy farmers. Each farmer, based on its type, assesses the feasibility of adopting soybean cultivation. The feasibility assessment depends on many interrelated factors, including price, production costs, yield, disease, drought (i.e., environmental stress), social pressure, group formations, learning and skills, risk-taking, subsidies, target profit margins, tolerance to bad experiences, etc. Moreover, after adopting soybean production, agents will reassess their performance. If their performance is unsatisfactory, an agent may opt out of soy production. Therefore, one of the main outcomes to look for in the model is the number of adopters over time.
The main agents are farmers. Generally, factors influencing farmers’ decision-making are divided into seven main areas: 1) external environmental factors, 2) cooperation and learning (with slight differences depending on whether they are arable or dairy farmers), 3) crop-specific factors, 4) economics, 5) support frameworks, 6) behavioral factors, and 7) the role of mobile toasters (applicable only to dairy farmers).
Moreover, factors not only influence decision-making but also interact with each other. Specifically, external environmental factors (i.e., stress) will result in lower yield and quality (protein content). The reducing effect, identified during participatory workshops, can reach 50 %. Skills can grow and improve yield; however, their growth has a limit and follows different learning curves depending on how individualistic a farmer is. During participatory workshops, it was identified that, contrary to cooperative farmers, individualistic farmers may learn faster and reach their limits more quickly. Furthermore, subsidies directly affect revenues and profit margins; however, their impact may disappear when they are removed. In the case of dairy farmers, mobile toasters play an important role, adding toasting and processing costs to those producing soy for their animal feed consumption.
Last but not least, behavioral factors directly influence the final adoption decision. For example, high risk-taking farmers may adopt faster, whereas more conservative farmers may wait for their neighbors to adopt first. Farmers may evaluate their success based on their own targets and may also consider other crops rather than soy.
Peer reviewed Descriptive Norm and Fraud Dynamics
Alexandra Eckert Matthias Meyer Christian Stindt | Published Tuesday, January 07, 2025The “Descriptive Norm and Fraud Dynamics” model demonstrates how fraudulent behavior can either proliferate or be contained within non-hierarchical organizations, such as peer networks, through social influence taking the form of a descriptive norm. This model expands on the fraud triangle theory, which posits that an individual must concurrently possess a financial motive, perceive an opportunity, and hold a pro-fraud attitude to engage in fraudulent activities (red agent). In the absence of any of these elements, the individual will act honestly (green agent).
The model explores variations in a descriptive norm mechanism, ranging from local distorted knowledge to global perfect knowledge. In the case of local distorted knowledge, agents primarily rely on information from their first-degree colleagues. This knowledge is often distorted because agents are slow to update their empirical expectations, which are only partially revised after one-to-one interactions. On the other end of the spectrum, local perfect knowledge is achieved by incorporating a secondary source of information into the agents’ decision-making process. Here, accurate information provided by an observer is used to update empirical expectations.
The model shows that the same variation of the descriptive norm mechanism could lead to varying aggregate fraud levels across different fraud categories. Two empirically measured norm sensitivity distributions associated with different fraud categories can be selected into the model to see the different aggregate outcomes.
Peer reviewed AgModel
Isaac Ullah | Published Friday, December 06, 2024AgModel is an agent-based model of the forager-farmer transition. The model consists of a single software agent that, conceptually, can be thought of as a single hunter-gather community (i.e., a co-residential group that shares in subsistence activities and decision making). The agent has several characteristics, including a population of human foragers, intrinsic birth and death rates, an annual total energy need, and an available amount of foraging labor. The model assumes a central-place foraging strategy in a fixed territory for a two-resource economy: cereal grains and prey animals. The territory has a fixed number of patches, and a starting number of prey. While the model is not spatially explicit, it does assume some spatiality of resources by including search times.
Demographic and environmental components of the simulation occur and are updated at an annual temporal resolution, but foraging decisions are “event” based so that many such decisions will be made in each year. Thus, each new year, the foraging agent must undertake a series of optimal foraging decisions based on its current knowledge of the availability of cereals and prey animals. Other resources are not accounted for in the model directly, but can be assumed for by adjusting the total number of required annual energy intake that the foraging agent uses to calculate its cereal and prey animal foraging decisions. The agent proceeds to balance the net benefits of the chance of finding, processing, and consuming a prey animal, versus that of finding a cereal patch, and processing and consuming that cereal. These decisions continue until the annual kcal target is reached (balanced on the current human population). If the agent consumes all available resources in a given year, it may “starve”. Starvation will affect birth and death rates, as will foraging success, and so the population will increase or decrease according to a probabilistic function (perturbed by some stochasticity) and the agent’s foraging success or failure. The agent is also constrained by labor caps, set by the modeler at model initialization. If the agent expends its yearly budget of person-hours for hunting or foraging, then the agent can no longer do those activities that year, and it may starve.
Foragers choose to either expend their annual labor budget either hunting prey animals or harvesting cereal patches. If the agent chooses to harvest prey animals, they will expend energy searching for and processing prey animals. prey animals search times are density dependent, and the number of prey animals per encounter and handling times can be altered in the model parameterization (e.g. to increase the payoff per encounter). Prey animal populations are also subject to intrinsic birth and death rates with the addition of additional deaths caused by human predation. A small amount of prey animals may “migrate” into the territory each year. This prevents prey animals populations from complete decimation, but also may be used to model increased distances of logistic mobility (or, perhaps, even residential mobility within a larger territory).
…
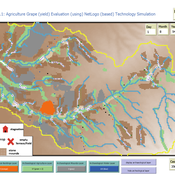
Peer reviewed Agriculture.Grape.yield.Evaluation.using.NetLogo.based.Technology.Simulation (AGENTS): A NetLogo agent-based model developed to assess viticulture efficiency in Byzantine Shivta.
Barak Garty Gil Gambash Guy BarOz Sharona T Levy | Published Friday, December 06, 2024AGENTS model is an agent-based computational framework designed to explore the socio-ecological and economic dynamics of agricultural production in the Byzantine Negev Highlands, with a focus on viticulture. It integrates historical, environmental, and social factors to simulate settlement sustainability, crop yields, and the impacts of varying climate conditions. The model is built in NetLogo and incorporates GIS-based topographical and hydrological data. Key features include the ability to assess climate impacts on crop profitability and settlement strategies, evaluate economic outputs of ancient vineyards, and simulate agent decision-making processes under diverse scenarios.
The AGENTS model is highly flexible, enabling users to simulate agricultural regimes with any two crops: one cash crop (a crop grown for profit, e.g., grapevines) and one staple crop (a crop grown for subsistence, e.g., wheat). While the default setup models viticulture and wheat cultivation in the Byzantine Negev Highlands, users can adapt the model to different environmental and socio-ecological contexts worldwide—both past and present.
Users can load external files to customize precipitation, evaporation, topography, and labor costs (measured as man-days per 0.1ha, converted to kg of wheat per model patch size area), and can also edit key parameters related to yield calculations. This includes modifying crop-specific yield formulas, soil and runoff indices, and any factors influencing crop performance. The model inherently simulates cash crops grown in floodplain regions and staple crops cultivated along riverbanks, providing a powerful tool to investigate societal resilience and responses to climate stressors across diverse environments.
…
Displaying 10 of 121 results decision making clear search