About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 72 results for "Luis Fernando Medina" clear search
Parental Investment Model (Aktipis and Fernandez-Duque)
Athena Aktipis | Published Saturday, July 17, 2010 | Last modified Saturday, April 27, 2013This is version 1 of the Parental Investment Model by Aktipis & Fernandez-Duque.
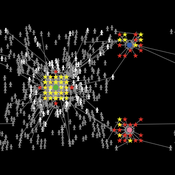
This project attempts to model how social media platforms recommend a user followers based on their interests, and how those individual interests change as a result of the influences from those they follow/are followed by.
We have three types of users on the platform:
Consumers (🔴), who update their interests based on who they’re following.
Creators (⬛), who update their interests based on who’s following them.
…
Imperfect knowledge and stable governance in democracies
Carlos M Fernández-Márquez Francisco Jose Vazquez Luis Fernando Medina | Published Tuesday, February 05, 2019In this paper we introduce an agent-based model of elections and government formation where voters do not have perfect knowledge about the parties’ ideological position. Although voters are boundedly rational, they are forward-looking in that they try to assess the likely impact of the different parties over the resulting government. Thus, their decision rules combine sincere and strategic voting: they form preferences about the different parties but deem some of them as inadmissible and try to block them from office. We find that the most stable and durable coalition governments emerge at intermediate levels of informational ambiguity. When voters have very poor information about the parties, their votes are scattered too widely, preventing the emergence of robust majorities. But also, voters with highly precise perceptions about the parties will cluster around tiny electoral niches with a similar aggregate effect.
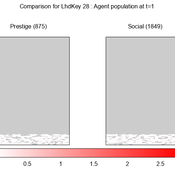
We provide a theory-grounded, socio-geographic agent-based model to present a possible explanation for human movement in the Adriatic region within the Cetina phenomenon.
Focusing on ideas of social capital theory from Piere Bordieu (1986), we implement agent mobility in an abstract geography based on cultural capital (prestige) and social capital (social position). Agents hold myopic representations of social (Schaff, 2016) and geographical networks and decide in a heuristic way on moving (and where) or staying.
The model is implemented in a fork of the Laboratory for Simulation Development (LSD), appended with GIS capabilities (Pereira et. al. 2020).
AMMA: Agent-based Model of the Media Arena
Annie Waldherr | Published Tuesday, February 11, 2014The AMMA simulates how news waves emerge in the mass media. Drawing on the ideas of public arena models and issue-attention cycles, it represents fundamental principles of public communication in a virtual media system.
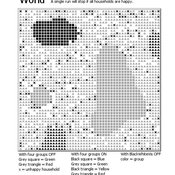
Introducing two extensions of Schelling's segregation model
Andreas Flache Carlos A. de Matos Fernandes | Published Monday, January 25, 2021Schelling famously proposed an extremely simple but highly illustrative social mechanism to understand how strong ethnic segregation could arise in a world where individuals do not necessarily want it. Schelling’s simple computational model is the starting point for our extensions in which we build upon Wilensky’s original NetLogo implementation of this model. Our two NetLogo models can be best studied while reading our chapter “Agent-based Computational Models” (Flache and de Matos Fernandes, 2021). In the chapter, we propose 10 best practices to elucidate how agent-based models are a unique method for providing and analyzing formally precise, and empirically plausible mechanistic explanations of puzzling social phenomena, such as segregation, in the social world. Our chapter addresses in particular analytical sociologists who are new to ABMs.
In the first model (SegregationExtended), we build on Wilensky’s implementation of Schelling’s model which is available in NetLogo library (Wilensky, 1997). We considerably extend this model, allowing in particular to include larger neighborhoods and a population with four groups roughly resembling the ethnic composition of a contemporary large U.S. city. Further features added concern the possibility to include random noise, and the addition of a number of new outcome measures tuned to highlight macro-level implications of the segregation dynamics for different groups in the agent society.
In SegregationDiscreteChoice, we further modify the model incorporating in particular three new features: 1) heterogeneous preferences roughly based on empirical research categorizing agents into low, medium, and highly tolerant within each of the ethnic subgroups of the population, 2) we drop global thresholds (%-similar-wanted) and introduce instead a continuous individual-level single-peaked preference function for agents’ ideal neighborhood composition, and 3) we use a discrete choice model according to which agents probabilistically decide whether to move to a vacant spot or stay in the current spot by comparing the attractiveness of both locations based on the individual preference functions.
…
PaCE Austria Pilot Model
Ruth Meyer | Published Tuesday, June 30, 2020The objective of building a social simulation in the Populism and Civic Engagement (PaCE) project is to study the phenomenon of populism by mapping individual level political behaviour and explain the influence of agents on, and their interdependence with the respective political parties. Voters, political parties and – to some extent – the media can be viewed as forming a complex adaptive system, in which parties compete for citizens’ votes, voters decide on which party to vote for based on their respective positions with regard to particular issues, and the media may influence the salience of issues in the public debate.
This is the first version of a model exploring voting behaviour in Austria. It focusses on modelling the interaction of voters and parties in a political landscape; the effects of the media are not yet represented. Austria was chosen as a case study because it has an established populist party (the “Freedom Party” FPO), which has even been part of the government over the years.
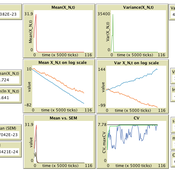
Population size limits the coefficient of variation in continuous traits affected by proportional copying error
Luke Premo | Published Thursday, June 18, 2020This version of the accumulated copying error (ACE) model is designed to address the following research question: how does finite population size (N) affect the coefficient of variation (CV) of a continuous cultural trait under the assumptions that the only source of copying error is visual perception error and that the continuous trait can take any positive value (i.e., it has no upper bound)? The model allows one to address this question while assuming the continuous trait is transmitted via vertical transmission, unbiased transmission, prestige biased transmission, mean conformist transmission, or median conformist transmission. By varying the parameter, p, one can also investigate the effect of population size under a mix of vertical and non-vertical transmission, whereby on average (1-p)N individuals learn via vertical transmission and pN individuals learn via either unbiased transmission, prestige biased transmission, mean conformist transmission, or median conformist transmission.
Opinion Leaders' Role in Innovation Diffusion
Peter Van Eck | Published Wednesday, March 10, 2010 | Last modified Saturday, April 27, 2013This model is used to investigate the role of opinion leader. More specifically: the influence of ‘innovative behavior’, ‘weigth of normative influence’, ‘better product judgment’, ‘number of opinion
Multi-agent model of the spread of climate change denial
Kalina Maria Piskorska Martin Takáč | Published Monday, March 03, 2025This NetLogo model simulates the spread of climate change beliefs within a population of individuals. Each believer has an initial belief level, which changes over time due to interactions with other individuals and exposure to media. The aim of the model is to identify possible methods for reducing climate change denial.
Displaying 10 of 72 results for "Luis Fernando Medina" clear search