About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 1209 results for "Lee-Ann Sutherland" clear search
Peer reviewed MADTOR: Model for Assessing Drug Trafficking Organizations Resilience
Deborah Manzi | Published Friday, February 23, 2024 | Last modified Friday, February 27, 2026Criminal organizations operate in complex changing environments. Being flexible and dynamic allows criminal networks not only to exploit new illicit opportunities but also to react to law enforcement attempts at disruption, enhancing the persistence of these networks over time. Most studies investigating network disruption have examined organizational structures before and after the arrests of some actors but have disregarded groups’ adaptation strategies.
MADTOR simulates drug trafficking and dealing activities by organized criminal groups and their reactions to law enforcement attempts at disruption. The simulation relied on information retrieved from a detailed court order against a large-scale Italian drug trafficking organization (DTO) and from the literature.
The results showed that the higher the proportion of members arrested, the greater the challenges for DTOs, with higher rates of disrupted organizations and long-term consequences for surviving DTOs. Second, targeting members performing specific tasks had different impacts on DTO resilience: targeting traffickers resulted in the highest rates of DTO disruption, while targeting actors in charge of more redundant tasks (e.g., retailers) had smaller but significant impacts. Third, the model examined the resistance and resilience of DTOs adopting different strategies in the security/efficiency trade-off. Efficient DTOs were more resilient, outperforming secure DTOs in terms of reactions to a single, equal attempt at disruption. Conversely, secure DTOs were more resistant, displaying higher survival rates than efficient DTOs when considering the differentiated frequency and effectiveness of law enforcement interventions on DTOs having different focuses in the security/efficiency trade-off.
Overall, the model demonstrated that law enforcement interventions are often critical events for DTOs, with high rates of both first intention (i.e., DTOs directly disrupted by the intervention) and second intention (i.e., DTOs terminating their activities due to the unsustainability of the intervention’s short-term consequences) culminating in dismantlement. However, surviving DTOs always displayed a high level of resilience, with effective strategies in place to react to threatening events and to continue drug trafficking and dealing.
A simulation tool for capability-based team task allocation in emergency-responce environments
Afsaneh Fatemi | Published Wednesday, March 16, 2011 | Last modified Saturday, April 27, 2013Its a multi agent simulation environment, provided using JADE/Java. It gets the number of agents and tasks, then divides the physical environment to some segments, and then runs a greedy capability-based coalition formation and task allocation algorithm to assign tasks to groups of agents and complete the tasks.
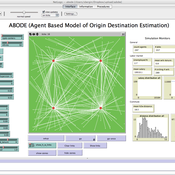
ABODE - Agent Based Model of Origin Destination Estimation
D Levinson | Published Monday, August 29, 2011 | Last modified Saturday, April 27, 2013The agent based model matches origins and destinations using employment search methods at the individual level.
Peer reviewed Population Genetics
Kristin Crouse | Published Thursday, February 08, 2018 | Last modified Wednesday, September 09, 2020This model simulates the mechanisms of evolution, or how allele frequencies change in a population over time.
Lake Anderson Revisited II
Klaus G. Troitzsch | Published Monday, June 28, 2021The purpose of this study is another agent-based replication of a System Dynamics model (Anderson,1973) where he analysed the dynamics of nutrient, biomass, oxygen and detritus in a model lake under conditions of artificial fertilising and policies to deal with the consequences of artificial fertilising.. A first replication (Möhring & Troitzsch,2001) added those agents to the original model that were necessary to move the role of the experimenter into the model, whereas this replication replaces the original lake with a collection of small elements between which biomass, nurtrents and oxygen are exchanged, adds rivers upstream and downstream as well as adjacent land divided into villages and populated with farms and industrial plants run by individual persons.
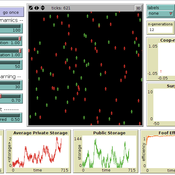
“Food for all” (FFD)
Andreas Angourakis José Manuel Galán Andrea L Balbo José Santos | Published Friday, April 25, 2014 | Last modified Monday, April 08, 2019“Food for all” (FFD) is an agent-based model designed to study the evolution of cooperation for food storage. Households face the social dilemma of whether to store food in a corporate stock or to keep it in a private stock.
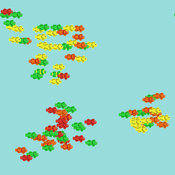
A simple behavioral model predicts the emergence of complex animal hierarchies
Takao Sasaki Zachary Joseph Shaffer Stephen Pratt Clint A Penick Jürgen Liebig | Published Tuesday, December 22, 2015We used our model to test how different combinations of dominance interactions present in H. saltator could result in linear, despotic, or shared hierarchies.
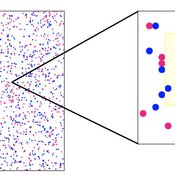
Human mate choice is a complex system
Paul Smaldino Jeffrey C Schank | Published Friday, February 08, 2013 | Last modified Saturday, April 27, 2013A general model of human mate choice in which agents are localized in space, interact with close neighbors, and tend to range either near or far. At the individual level, our model uses two oft-used but incompletely understood decision rules: one based on preferences for similar partners, the other for maximally attractive partners.
06 EiLab V1.36 – Entropic Index Laboratory
Garvin Boyle | Published Saturday, January 31, 2015 | Last modified Friday, April 14, 2017EiLab explores the role of entropy in simple economic models. EiLab is one of several models exploring the dynamics of sustainable economics – PSoup, ModEco, EiLab, OamLab, MppLab, TpLab, and CmLab.
Asymmetric two-sided matching
Naoki Shiba | Published Wednesday, January 09, 2013 | Last modified Tuesday, May 28, 2013This model is an extended version of the matching problem including the mate search problem, which is the generalization of a traditional optimization problem. The matching problem is extended to a form of asymmetric two-sided matching problem.
Displaying 10 of 1209 results for "Lee-Ann Sutherland" clear search