About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 28 results for "Maria Beatrice Pairotti" clear search
Alternative scenarios of green consumption in Italy: an empirically grounded model.
Giangiacomo Bravo Elena Vallino Alessandro K Cerutti Maria Beatrice Pairotti | Published Thursday, March 28, 2013 | Last modified Saturday, April 27, 2013We provide a full description of the model following the ODD protocol (Grimm et al. 2010) in the attached document. The model is developed in NetLogo 5.0 (Wilenski 1999).
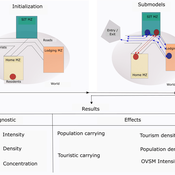
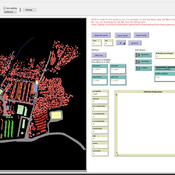
Peer reviewed ABM Overtourism Santa Marta
Janwar Moreno | Published Monday, October 23, 2023This model presents the simulation model of a city in the context of overtourism. The study area is the city of Santa Marta in Colombia. The purpose is to illustrate the spatial and temporal distribution of population and tourists in the city. The simulation analyzes emerging patterns that result from the interaction between critical components in the touristic urban system: residents, urban space, touristic sites, and tourists. The model is an Agent-Based Model (ABM) with the GAMA software. Also, it used public input data from statistical centers, geographical information systems, tourist websites, reports, and academic articles. The ABM includes assessing some measures used to address overtourism. This is a field of research with a low level of analysis for destinations with overtourism, but the ABM model allows it. The results indicate that the city has a high risk of overtourism, with spatial and temporal differences in the population distribution, and it illustrates the effects of two management measures of the phenomenon on different scales. Another interesting result is the proposed tourism intensity indicator (OVsm), taking into account that the tourism intensity indicators used by the literature on overtourism have an overestimation of tourism pressures.
AIforGoodSimulator - Modeling Covid-19 Spread and Potential Interventions in Refugee Camps
Shyaam Ramkumar Woi Sok Oh | Published Thursday, March 18, 2021The Netlogo model is a conceptualization of the Moria refugee camp, capturing the household demographics of refugees in the camp, a theoretical friendship network based on values, and an abstraction of their daily activities. The model then simulates how Covid-19 could spread through the camp if one refugee is exposed to the virus, utilizing transmission probabilities and the stages of disease progression of Covid-19 from susceptible to exposed to asymptomatic / symptomatic to mild / severe to recovered from literature. The model also incorporates various interventions - PPE, lockdown, isolation of symptomatic refugees - to analyze how they could mitigate the spread of the virus through the camp.
Seeding for information transmission in social networks
Beatrice Nöldeke Ulrike Grote Etti Winter | Published Tuesday, November 03, 2020This model simulates different seeding strategies for information diffusion in a social network adjusted to a case study area in rural Zambia. It systematically evaluates different criteria for seed selection (centrality measures and hierarchy), number of seeds, and interaction effects between seed selection criteria and set size.
Biodiversity and Adoption of Small-scale Agroforestry in Rwanda (BASAR)
Beatrice Nöldeke Etti Winter Elisée Bahati Ntawuhiganayo | Published Friday, July 15, 2022The BASAR model aims to investigate different approaches to describe small-scale farmers’ decision-making in the context of diversified agroforestry adoption in rural Rwanda. Thereby, it compares random behaviour with perfect rationality (non-discounted and discounted utility maximization), bounded rationality (satisficing and fast and frugal decision tree heuristics), Theory of Planned Behaviour, and a probabilistic regression-based approach. It is aimed at policy-makers, extension agents, and cooperatives to better understand how rural farmers decide about implementing innovative agricultural practices such as agroforestry and at modelers to support them in selecting an approach to represent human decision-making in ABMs of Social-Ecological Systems. The overall objective is to identify a suitable approach to describe human decision-making and therefore improve forecasts of adoption rates and support the development and implementation of interventions that aim to raise low adoption rates.
SAFARI: Simulating Agroforestry Adoption in Rural Indonesia
Beatrice Nöldeke Etti Winter Yves Laumonier Trifosa Simamora | Published Tuesday, July 20, 2021The Simulating Agroforestry Adoption in Rural Indonesia (SAFARI) model aims at exploring the adoption of illipe rubber agroforestry systems by farming households in the case study region in rural Indonesia. Thereby, the ABM simulates the interdependencies of agroforestry systems and local livelihoods, income, land use, biodiversity, and carbon fixation. The model contrasts development paths without agroforestry (business as usual (BAU) scenario), corresponding to a scenario where the government promotes rubber monoculture, with the introduction of illipe rubber agroforestry systems (IRA scenario) as an alternative. It aims to support policy-makers to assess the potential of IRA over larger temporal and spatial scales.
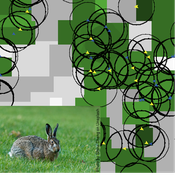
Mitigating bioenergy-driven biodiversity decline: a modelling approach with the European brown hare
Volker Grimm Maria Langhammer | Published Wednesday, November 13, 2019 | Last modified Tuesday, November 24, 2020The model is designed to analyse the effects of mitigation measures on the European brown hare (Lepus europaeus), which is directly affected by ongoing land use change and has experienced widespread decline throughout Europe since the 1960s. As an input, we use two 4×4 km large model landscapes, which were generated by a landscape generator based on real field sizes and crop proportions and differed in average field size and crop composition. The crops grown annually are evaluated in terms of forage suitability, breeding suitability and crop richness for the hare. Six mitigation scenarios are implemented, defined by a 10 % increase in: (1) mixed silphie, (2) miscanthus, (3) grass-clover ley, (4) alfalfa, (5) set-aside, and (6) general crop richness. The model shows that that both landscape configuration and composition have a significant effect on hare population development, which responds particularly strongly to compositional changes.
Peer reviewed Behavior changes through influence
Daria Soboleva | Published Friday, August 30, 2024The model is designed to simulate the behavior and decision-making processes of individuals (agents) in a social network. It aims to represent the changes in individual probability to take any action based on changes in attributes. The action is anything that can be reasonably influenced by the three influencing methods implemented in this model: peer pressure, social media, and state campaigns, and for which the user has a decision-making model. The model is implemented in the multi-agent programmable environment NetLogo 6.3.0.
Vulnerability of Cooperation Due to Limited Vision
Marco Janssen | Published Thursday, December 02, 2010 | Last modified Saturday, April 27, 2013This model describes the consequences of limited vision of agents in harvesting a common resource. We show the vulnerability of cooperation due to reduced visibility of the resource and other agents.
Multi-agent model of the spread of climate change denial
Kalina Maria Piskorska Martin Takáč | Published Monday, March 03, 2025This NetLogo model simulates the spread of climate change beliefs within a population of individuals. Each believer has an initial belief level, which changes over time due to interactions with other individuals and exposure to media. The aim of the model is to identify possible methods for reducing climate change denial.
Displaying 10 of 28 results for "Maria Beatrice Pairotti" clear search