About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 34 results for 'Coen Van Wagenberg'
Foragers to Farmers
Michael Storozum Elske van der Vaart Tim Dorscheidt Nicolas Gauthier | Published Monday, July 22, 2024This model is represents an effort to replicate one of the first attempts (van der Vaart 2006) to develop an agent based model of agricultural origins using principles and equations drawn from human behavioral ecology. We have taken one theory of habitat choice (Ideal Free Distribution) and applied it to human behavioral adaptations to differences in resource quality of different habitats.
DARTS: modelling effects of shocks on global, regional, urban and rural food security
Pepijn van Oort Hubert Fonteijn Geerten Hengeveld | Published Tuesday, June 18, 2024Food trade networks represent a complex system where food is periodically produced in different regions of the world. Food is continuously stocked and traded. Food security in a globalised world is vulnerable to shocks. We present DARTS, a new agent based model that models monthly dynamics of food production, trade, stocking, consumption and food security for different interconnected world regions and a city state. Agents in different regions differ in their harvest seasons, wealth (rich and poor), degree of urbanisation and connection to domestic and global markets. DARTS was specifically designed to model direct and indirect effects of shocks in the food system. We introduce a new typology of 6 distinct shock types and analyse their impact on food security, modelling local and global effects and short term and longer term effects. An second important scientific novelty of the model is that DARTS can also model indirect effects of shocks (cascading in space and in time, lag effects due to trade and food stock buffering). A third important scientific novelty of the model is its’ capability of modelling food security at different scales, in which the rural/urban divide and differences in (intra-annually varying) production and trade connections play a key role. At the time of writing DARTS is yet insufficiently parameterised for accurate prediction for real world regions and cities. Simulations for a hypothetical in silico world with 3 regions and a city state show that DARTS can reproduce rich and complex dynamics with analogues in the real world. The scientific interest is more on deepening insight in process dynamics and chains of events that lead to ultimate shock effects on food security.
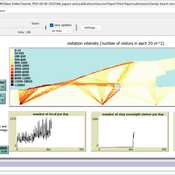
Sandy Beach Visitor Flow: An Agent-Based Model
Elham Bakhshianlamouki | Published Thursday, March 14, 2024The model is intended to simulate visitor spatial and temporal dynamics, encompassing their numbers, activities, and distribution along a coastline influenced by beach landscape design. Our primary focus is understanding how the spatial distribution of services and recreational facilities (e.g., beach width, entrance location, recreational facilities, parking availability) impacts visitation density. Our focus is not on tracking the precise visitation density but rather on estimating the areas most affected by visitor activity. This comprehension allows for assessing the diverse influences of beach layouts on spatial visitor density and, consequently, on the landscape’s biophysical characteristics (e.g., vegetation, fauna, and sediment features).
Peer reviewed HUMLAND: HUMan impact on LANDscapes agent-based model
Anastasia Nikulina Katharine MacDonald Anhelina Zapolska Maria Antonia Serge Marco Davoli Dave van Wees Fulco Scherjon | Published Monday, October 16, 2023The HUMan impact on LANDscapes (HUMLAND) model has been developed to track and quantify the intensity of different impacts on landscapes at the continental level. This agent-based model focuses on determining the most influential factors in the transformation of interglacial vegetation with a specific emphasis on burning organized by hunter-gatherers. HUMLAND integrates various spatial datasets as input and target for the agent-based model results. Additionally, the simulation incorporates recently obtained continental-scale estimations of fire return intervals and the speed of vegetation regrowth. The obtained results include maps of possible scenarios of modified landscapes in the past and quantification of the impact of each agent, including climate, humans, megafauna, and natural fires.
Peer reviewed Co-adoption of low-carbon household energy technologies
Mart van der Kam Maria Lagomarsino Elie Azar Ulf Hahnel David Parra | Published Tuesday, August 29, 2023 | Last modified Friday, February 23, 2024The model simulates the diffusion of four low-carbon energy technologies among households: photovoltaic (PV) solar panels, electric vehicles (EVs), heat pumps, and home batteries. We model household decision making as the decision marking of one person, the agent. The agent decides whether to adopt these technologies. Hereby, the model can be used to study co-adoption behaviour, thereby going beyond traditional diffusion models that focus on the adop-tion of single technologies. The combination of these technologies is of particular interest be-cause (1) using the energy generated by PV solar panels for EVs and heat pumps can reduce emissions associated with transport and heating, respectively, and (2) EVs, heat pumps, and home batteries can help to integrate PV solar panels in local electricity grids by offering flexible demand (EVs and heat pumps) and energy storage (home batteries and EVs), thereby reducing grid impacts and associated upgrading costs.
The purpose of the model is to represent realistic adoption and co-adoption behaviour. This is achieved by grounding the decision model on the risks-as-feelings model (Loewenstein et al., 2001), theory from environmental and social psychology, and empirically informing agent be-haviour by survey-data among 1469 people in the Swiss region Romandie.
The model can be used to construct scenarios for the diffusion of the four low-carbon energy technologies depending on different contexts, and as a virtual experimentation environment for ex ante evaluation of policy interventions to stimulate adoption and co-adoption.
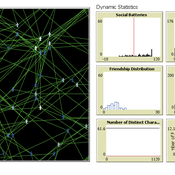
The Friendship Field
Eva Timmer Chrisja van de Kieft | Published Thursday, May 26, 2022 | Last modified Tuesday, August 30, 2022The Friendship Field model aims at modelling friendship formation based on three factors: Extraversion, Resemblance and Status, where social interaction is motivated by the Social Battery. Social Battery is one’s energy and motivation to engage in social contact. Since social contact is crucial for friendship formation, the model included Social Battery to affect social interactions. To our best knowledge, Social Battery is a yet unintroduced concept in research while it is a dynamic factor influencing the social interaction besides one’s characteristics. Extraverts’ Social Batteries charge while interacting and exhaust while being alone. Introverts’ Social Batteries charge while being alone and exhaust while interacting. The aim of the model is to illustrate the concept of Social Battery. Moreover, the Friendship Field shows patterns regarding Extraversion, Resemblance and Status including the mere-exposure effect and friendship by similarity. For the implementation of Status, Kemper’s status-power theory is used. The concept of Social Battery is also linked to Kemper’s theory on the organism as reference group. By running the model for a year (3 interactions moments per day), the friendship dynamics over time can be studied.
We presented the model at the Social Simulation Conference 2022.
MiniDemographicABM.jl: A simplified agent-based demographic model of the UK
Atiyah Elsheikh | Published Friday, July 28, 2023 | Last modified Tuesday, December 12, 2023This package implements a simplified artificial agent-based demographic model of the UK. Individuals of an initial population are subject to ageing, deaths, births, divorces and marriages. A specific case-study simulation is progressed with a user-defined simulation fixed step size on a hourly, daily, weekly, monthly basis or even an arbitrary user-defined clock rate. While the model can serve as a base model to be adjusted to realistic large-scale socio-economics, pandemics or social interactions-based studies mainly within a demographic context, the main purpose of the model is to explore and exploit capabilities of the state-of-the-art Agents.jl Julia package as well as other ecosystem of Julia packages like GlobalSensitivity.jl. Code includes examples for evaluating global sensitivity analysis using Morris and Sobol methods and local sensitivity analysis using OFAT and OAT methods. Multi-threaded parallelization is enabled for improved runtime performance.
Modelling value change; An exploratory approach
Tristan de Wildt Ibo van de Poel | Published Tuesday, June 20, 2023 | Last modified Tuesday, December 12, 2023This model has been developed together with the publication ‘Modelling Value Change - An Exploratory Approach’
Value change and moral change have increasingly become topics of interest in the philosophical literature. Several theoretical accounts have been proposed. Such accounts are usually based on certain theoretical and conceptual assumptions and their strengths and weaknesses are often hard to determine and compare, also because they are based on limited empirical evidence.
We propose that a step forward can be made with the help of agent-based modelling (ABM). ABM can be used to investigate whether a simulation model based on a specific account of value change can reproduce relevant phenomena. To illustrate this approach, we built a model based on the pragmatist account of value change proposed in van de Poel and Kudina (2022). We show that this model can reproduce four relevant phenomena, namely 1) the inevitability and stability of values, 2) how different societies may react differently to external shocks, 3) moral revolutions, and 4) lock-in.
Gender Disparity in COVID-19’s Impact on Academic Careers: An Agent-Based Model
Mai Trinh Chantal van Esch | Published Tuesday, September 26, 2023Prior to COVID-19, female academics accounted for 45% of assistant professors, 37% of associate professors, and 21% of full professors in business schools (Morgan et al., 2021). The pandemic arguably widened this gender gap, but little systemic data exists to quantify it. Our study set out to answer two questions: (1) How much will the COVID-19 pandemic have impacted the gender gap in U.S. business school tenured and tenure-track faculty? and (2) How much will institutional policies designed to help faculty members during the pandemic have affected this gender gap? We used agent-based modeling coupled with archival data to develop a simulation of the tenure process in business schools in the U.S. and tested how institutional interventions would affect this gender gap. Our simulations demonstrated that the gender gap in U.S. business schools was on track to close but would need further interventions to reach equality (50% females). In the long-term picture, COVID-19 had a small impact on the gender gap, as did dependent care assistance and tenure extensions (unless only women received tenure extensions). Changing performance evaluation methods to better value teaching and service activities and increasing the proportion of female new hires would help close the gender gap faster.
Peer reviewed ABM to create populations with realistic Big Five Personality Trait Expressions
Michael Vogrin | Published Tuesday, May 30, 2023This model aims at creating agent populations that have “personalities”, as described by the Big Five Model of Personality. The expression of the Big Five in the agent population has the following properties, so that they resemble real life populations as closely as possible:
-The population mean of each trait is 0.5 on a scale from 0 to 1.
-The population-wide distribution of each trait approximates a normal distribution.
-The intercorrelations of the Big Five are close to those observed in the Literature.
The literature used to fit the model was a publication by Dimitri van der Linden, Jan te Nijenhuis, and Arnold B. Bakker:
…
Displaying 10 of 34 results for 'Coen Van Wagenberg'