About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 16 results War clear search
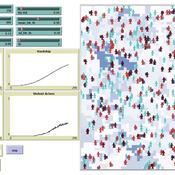
Simulating Climate Stress and Social Instability: An Agent-Based Model of Ecosystem Degradation and Violence in Coastal Communities
Jacopo A. Baggio hurtado-valdivieso | Published Sunday, April 12, 2026This model is an agent-based simulation designed to explore how climate-induced environmental degradation can contribute to the emergence of social violence in coastal communities that depend heavily on ecosystem services for their livelihoods. The model represents a coupled social–ecological system in which environmental shocks—such as sea level rise and marine ecosystem decline—affect local economic conditions, food security, and community stability.
Agents in the model represent individuals whose livelihoods depend on coastal ecosystems. Environmental degradation reduces ecosystem productivity and increases economic hardship, which can lead to the formation of grievances among agents. The model incorporates behavioral thresholds that determine how individuals respond to hardship and perceived injustice. Under certain conditions—particularly when institutional capacity and law enforcement effectiveness are limited—these grievances may escalate into violent behavior.
The simulation allows users to explore how different climate scenarios, levels of ecosystem degradation, livelihood dependence, and institutional responses influence the probability of social instability and violence. By modeling the interactions between environmental stress, socio-economic vulnerability, and governance capacity, the model provides a computational framework for examining potential pathways linking climate change and conflict in coastal social–ecological systems.
…
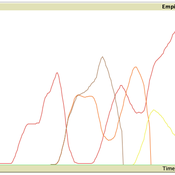
Replica of Turchin's (2003) Metaethnic Frontier model
Paul Smaldino | Published Sunday, February 15, 2026In his 2003 book, Historical Dynamics (ch. 4), Turchin describes and briefly analyzes a spatial ABM of his metaethnic frontier theory, which is essentially a formalization of a theory by Ibn Khaldun in the 14th century. In the model, polities compete with neighboring polities and can absorb them into an empire. Groups possess “asabiya”, a measure of social solidarity and a sense of shared purpose. Regions that share borders with other groups will have increased asabiya do to salient us vs. them competition. High asabiya enhances the ability to grow, work together, and hence wage war on neighboring groups and assimilate them into an empire. The larger the frontier, the higher the empire’s asabiya.
As an empire expands, (1) increased access to resources drives further growth; (2) internal conflict decreases asabiya among those who live far from the frontier; and (3) expanded size of the frontier decreases ability to wage war along all frontiers. When an empire’s asabiya decreases too much, it collapses. Another group with more compelling asabiya eventually helps establish a new empire.
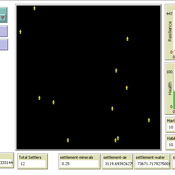
An Agent-Based Model of Space Settlements
Anamaria Berea | Published Wednesday, August 09, 2023 | Last modified Wednesday, November 01, 2023Background: Establishing a human settlement on Mars is an incredibly complex engineering problem. The inhospitable nature of the Martian environment requires any habitat to be largely self-sustaining. Beyond mining a few basic minerals and water, the colonizers will be dependent on Earth resupply and replenishment of necessities via technological means, i.e., splitting Martian water into oxygen for breathing and hydrogen for fuel. Beyond the technical and engineering challenges, future colonists will also face psychological and human behavior challenges.
Objective: Our goal is to better understand the behavioral and psychological interactions of future Martian colonists through an Agent-Based Modeling (ABM simulation) approach. We seek to identify areas of consideration for planning a colony as well as propose a minimum initial population size required to create a stable colony.
Methods: Accounting for engineering and technological limitations, we draw on research regarding high performing teams in isolated and high stress environments (ex: submarines, Arctic exploration, ISS, war) to include the 4 NASA personality types within the ABM. Interactions between agents with different psychological profiles are modeled at the individual level, while global events such as accidents or delays in Earth resupply affect the colony as a whole.
Results: From our multiple simulations and scenarios (up to 28 Earth years), we found that an initial population of 22 was the minimum required to maintain a viable colony size over the long run. We also found that the Agreeable personality type was the one more likely to survive.
Conclusion We developed a simulation with easy to use GUI to explore various scenarios of human interactions (social, labor, economic, psychological) on a future colony on Mars. We included technological and engineering challenges, but our focus is on the behavioral and psychological effects on the sustainability of the colony on the long run. We find, contrary to other literature, that the minimum number of people with all personality types that can lead to a sustainable settlement is in the tens and not hundreds.
Scholars have written extensively about hierarchical international order, on the one hand, and war on the other, but surprisingly little work systematically explores the connection between the two. This disconnect is all the more striking given that empirical studies have found a strong relationship between the two. We provide a generative computational network model that explains hierarchy and war as two elements of a larger recursive process: The threat of war drives the formation of hierarchy, which in turn shapes states’ incentives for war. Grounded in canonical theories of hierarchy and war, the model explains an array of known regularities about hierarchical order and conflict. Surprisingly, we also find that many traditional results of the IR literature—including institutional persistence, balancing behavior, and systemic self-regulation—emerge from the interplay between hierarchy and war.
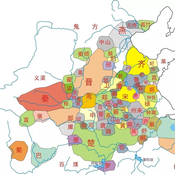
Unification-Conditions-of-Civilization-Patterns-Multi-Agent-Modeling-of-Human-History
zhuo zhang | Published Friday, May 27, 2022 | Last modified Sunday, May 29, 2022The model of Chinese and Western civilization patterns can help understand how civilizations formed, how they evolved by themselves, and the difference between the unity of China and the disunity of the Western. The previous research had examined historical phenomena about civilization patterns with subjective, static, local, and inductive methods. Therefore, we propose a general model of history dynamics for civilizations pattern, which contains both China and the West, to improve our understanding of civilization formation and the factors influencing the pattern of civilization. And at the same time, the model is used to find the boundary conditions of two different patterns.
Competitive Arousal Agent Based Model
Zoé Chollet | Published Friday, May 13, 2022What is it?
This model demonstrates a very simple bidding market where buyers try to acquire a desired item at the best price in a competitive environment
…
ThomondSim
Vinicius Marino Carvalho | Published Monday, April 25, 2022 | Last modified Friday, May 12, 2023ThomondSim is a simulation of the political and economic landscape of the medieval kingdom of Thomond, southwestern Ireland, between 1276 and 1318.
Its goal is to analyze how deteriorating environmental and economic conditions caused by the Little Ice Age (LIA), the Great European Famine of 1315-1322, and wars between England and Scotland affected the outcomes of a local war involving Gaelic and English aristocratic lineages.
This ABM attempts to model both the effects of devastation on the human environment and the modus operandi of late-medieval war and diplomacy.
The model is the digital counterpart of the science discovery board game The Triumphs of Turlough. Its procedures closely correspond to the game’s mechanics, to the point that ToT can be considered an interactive, analog version of this ABM.
Space colonization
allagonne | Published Wednesday, January 05, 2022Agent-Based-Modeling - space colonization
ask me for the .nlogo model
WHAT IS IT?
The goal of this project is to simulate with NetLogo (v6.2) a space colonization of humans, starting from Earth, into the Milky Way.
HOW IT WORKS
…
Rebel Group Protection Rackets
Gerd Wagner Luis Gustavo Nardin Kamil C. Klosek Frances Duffy | Published Wednesday, December 04, 2019System Narrative
How do rebel groups control territory and engage with the local economy during civil war? Charles Tilly’s seminal War and State Making as Organized Crime (1985) posits that the process of waging war and providing governance resembles that of a protection racket, in which aspiring governing groups will extort local populations in order to gain power, and civilians or businesses will pay in order to ensure their own protection. As civil war research increasingly probes the mechanisms that fuel local disputes and the origination of violence, we develop an agent-based simulation model to explore the economic relationship of rebel groups with local populations, using extortion racket interactions to explain the dynamics of rebel fighting, their impact on the economy, and the importance of their economic base of support. This analysis provides insights for understanding the causes and byproducts of rebel competition in present-day conflicts, such as the cases of South Sudan, Afghanistan, and Somalia.
Model Description
The model defines two object types: RebelGroup and Enterprise. A RebelGroup is a group that competes for power in a system of anarchy, in which there is effectively no government control. An Enterprise is a local civilian-level actor that conducts business in this environment, whose objective is to make a profit. In this system, a RebelGroup may choose to extort money from Enterprises in order to support its fighting efforts. It can extract payments from an Enterprise, which fears for its safety if it does not pay. This adds some amount of money to the RebelGroup’s resources, and they can return to extort the same Enterprise again. The RebelGroup can also choose to loot the Enterprise instead. This results in gaining all of the Enterprise wealth, but prompts the individual Enterprise to flee, or leave the model. This reduces the available pool of Enterprises available to the RebelGroup for extortion. Following these interactions the RebelGroup can choose to AllocateWealth, or pay its rebel fighters. Depending on the value of its available resources, it can add more rebels or expel some of those which it already has, changing its size. It can also choose to expand over new territory, or effectively increase its number of potential extorting Enterprises. As a response to these dynamics, an Enterprise can choose to Report expansion to another RebelGroup, which results in fighting between the two groups. This system shows how, faced with economic choices, RebelGroups and Enterprises make decisions in war that impact conflict and violence outcomes.
RefugeePathSIM Model
Liliana Perez Saeed Harati Guillaume Arnoux Hébert | Published Thursday, October 11, 2018 | Last modified Tuesday, October 16, 2018RefugeePathSIM is an agent-based model to simulate the movement behavior of refugees in order to identify pathways of forced migration under crisis. The model generates migrants and lets them leave conflict areas for a destination that they choose based on their characteristics and desires. RefugeePathSIM has been developed and applied in a study of the Syrian war, using monthly data in years 2011-2015.
Displaying 10 of 16 results War clear search