About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 1188 results for "Aad Kessler" clear search
Diffusion of Eco-Innovation through Inter-firm Network Targeting: An Agent-Based Model
apyka Flaminio Squazzoni Shyaam Ramkumar Matthias Mueller | Published Monday, January 10, 2022This model is developed as a theoretical agent-based model to study the general phenomena of network-based targeting strategies on eco-innovation adoption and diffusion through inter-firm networks.
Peer reviewed INOvPOP
Aniruddha Belsare | Published Wednesday, June 01, 2022 | Last modified Wednesday, July 10, 2024INOvPOP is designed to simulate population dynamics (abundance, sex-age composition and distribution in the landscape) of white-tailed deer (Odocoileus virginianus) for selected Indiana counties. Updated for netLogo 6.4.0
Agent-based Modeling of Evolving Intergovernmental Networks
Sungho Lee | Published Thursday, January 29, 2009 | Last modified Saturday, April 27, 2013This agent-based model using ‘Blanche’ software provides policy-makers with a simulation-based demonstration illustrating how autonomous agents network and operate complementary systems in a decentral
CPNorm
Ruth Meyer | Published Sunday, June 04, 2017 | Last modified Tuesday, June 13, 2017CPNorm is a model of a community of harvesters using a common pool resource where adhering to the optimal extraction level has become a social norm. The model can be used to explore the robustness of norm-driven cooperation in the commons.
Ger Grouper
Stefani Crabtree | Published Tuesday, January 05, 2021A “Ger” is a yurt style house used by pastoralists in Mongolia. This model simulates seasonal movements, fission/fusion dynamics, social interaction between households and how these relate to climate impacts.
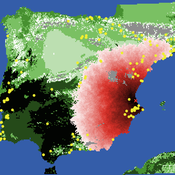
Neolithic Spread Model Version 1.0
Sean Bergin Salvador Pardo Gordo Joan Bernabeu Auban Michael Barton | Published Thursday, December 11, 2014 | Last modified Monday, December 31, 2018This model simulates different spread hypotheses proposed for the introduction of agriculture on the Iberian peninsula. We include three dispersal types: neighborhood, leapfrog, and ideal despotic distribution (IDD).
The Effect of Different Governmental Pandemic Control Measures on the Spread of a Virus Disease
Chiara Letter | Published Wednesday, January 26, 2022In this model, the spread of a virus disease in a network consisting of school pupils, employed, and umemployed people is simulated. The special feature in this model is the distinction between different types of links: family-, friends-, school-, or work-links. In this way, different governmental measures can be implemented in order to decelerate or stop the transmission.
NetLogo-R-Example for the Inititialisation of Agents with Correlated Random Numbers
Danilo Saft | Published Friday, February 14, 2014 | Last modified Monday, April 08, 2019This is a short NetLogo example demonstrating how to initialize 500 agents with 4 correlated parameters each with random values by doing the necessary calculations in the program “R” and retrieving the results.
Peer reviewed A Macroeconomic Model of a Closed Economy
Ian Stuart | Published Saturday, May 08, 2021 | Last modified Wednesday, June 23, 2021This model/program presents a “three industry model” that may be particularly useful for macroeconomic simulations. The main purpose of this program is to demonstrate a mechanism in which the relative share of labor shifts between industries.
Care has been taken so that it is written in a self-documenting way so that it may be useful to anyone that might build from it or use it as an example.
This model is not intended to match a specific economy (and is not calibrated to do so) but its particular minimalist implementation may be useful for future research/development.
…
Evaluating Government's Policies on Promoting Smart Metering Diffusion in Retail Electricity Markets
Tao Zhang | Published Monday, December 07, 2009 | Last modified Saturday, April 27, 2013This model is a market game for evaluating the effectiveness of the UK government’s 2008-2010 policy on promoting smart metering in the UK retail electricity market. We break down the policy into four
Displaying 10 of 1188 results for "Aad Kessler" clear search