About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 1 of 1 results NetworkX clear search
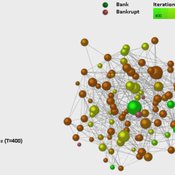
Dynamic Interbank Network Simulator
Valentina Guleva | Published Wednesday, November 23, 2016 | Last modified Monday, April 13, 2020The model provides instruments for the simulation of interbank network evolution. There are tools for dynamic network analysis, allowing to evaluate graph topological invariants, thermodynamic network features and combinational node-based features.