About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 8 of 8 results violence clear
Social Identity Model of Protest Emergence (SIMPE)
Cristina Chueca Del Cerro | Published Friday, March 17, 2023The Social Identity Model of Protest Emergence (SIMPE), an agent-based model of national identity and protest mobilisations.
I developed this model for my PhD project, “Polarisation and Protest Mobilisation Around Secessionist Movements: an Agent-Based Model of Online and Offline Social Networks”, at the University of Glasgow (2019-2023).
The purpose of this model is to simulate protest emergence in a given country where there is an independence movement, fostering the self-categorisation process of national identification. In order to contextualised SIMPE, I have used Catalonia, where an ongoing secessionist movement since 2011 has been present, national identity has shown signs of polarisation, and where numerous mobilisations have taken place over the last decade. Data from the Catalan Centre of Opinion Studies (CEO) has been used to inform some of the model parameters.
…
Police funding: legitimacy and hardship
Jack Mitcham | Published Sunday, February 27, 2022An extension of Epstein’s (2002) model for civil violence and Fonoberova et al’s (2012) extension of Epstein’s model. Uses heterogeneous hardship values and dynamic legitimacy values. Models public funding decisions between police and social welfare.
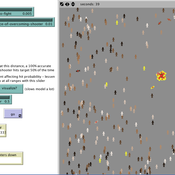
Hybrid agent-based methodology for testing response protocols
Fernando Sancho Caparrini | Published Wednesday, February 03, 2021In recent years we have seen multiple incidents with a large number of people injured and killed by one or more armed attackers. Since this type of violence is difficult to predict, detecting threats as early as possible allows to generate early warnings and reduce response time. In this context, any tool to check and compare different action protocols can be a further step in the direction of saving lives. Our proposal combines features from continuous and discrete models to obtain the best of both worlds in order to simulate large and crowded spaces where complex behavior individuals interact. With this proposal we aim to provide a tool for testing different security protocols under several emergency scenarios, where spaces, hazards, and population can be customized. Finally, we use a proof of concept implementation of this model to test specific security protocols under emergency situations for real spaces. Specifically, we test how providing some users of a university college with an app that informs about the type and characteristics of the ongoing hazard, affects in the safety performance.
VIDA: A simulation model of domestic VIolence in times of social DistAncing
B Furtado | Published Monday, January 11, 2021Violence against women occurs predominantly in the family and domestic context. The COVID-19 pandemic led Brazil to recommend and, at times, impose social distancing, with the partial closure of economic activities, schools, and restrictions on events and public services. Preliminary evidence shows that intense co- existence increases domestic violence, while social distancing measures may have prevented access to public services and networks, information, and help. We propose an agent-based model (ABM), called VIDA, to illustrate and examine multi-causal factors that influence events that generate violence. A central part of the model is the multi-causal stress indicator, created as a probability trigger of domestic violence occurring within the family environment. Two experimental design tests were performed: (a) absence or presence of the deterrence system of domestic violence against women and measures to increase social distancing. VIDA presents comparative results for metropolitan regions and neighbourhoods considered in the experiments. Results suggest that social distancing measures, particularly those encouraging staying at home, may have increased domestic violence against women by about 10%. VIDA suggests further that more populated areas have comparatively fewer cases per hundred thousand women than less populous capitals or rural areas of urban concentrations. This paper contributes to the literature by formalising, to the best of our knowledge, the first model of domestic violence through agent-based modelling, using empirical detailed socioeconomic, demographic, educational, gender, and race data at the intraurban level (census sectors).
Rebel Group Protection Rackets
Frances Duffy Kamil C. Klosek Luis Nardin Gerd Wagner | Published Wednesday, December 04, 2019System Narrative
How do rebel groups control territory and engage with the local economy during civil war? Charles Tilly’s seminal War and State Making as Organized Crime (1985) posits that the process of waging war and providing governance resembles that of a protection racket, in which aspiring governing groups will extort local populations in order to gain power, and civilians or businesses will pay in order to ensure their own protection. As civil war research increasingly probes the mechanisms that fuel local disputes and the origination of violence, we develop an agent-based simulation model to explore the economic relationship of rebel groups with local populations, using extortion racket interactions to explain the dynamics of rebel fighting, their impact on the economy, and the importance of their economic base of support. This analysis provides insights for understanding the causes and byproducts of rebel competition in present-day conflicts, such as the cases of South Sudan, Afghanistan, and Somalia.
Model Description
The model defines two object types: RebelGroup and Enterprise. A RebelGroup is a group that competes for power in a system of anarchy, in which there is effectively no government control. An Enterprise is a local civilian-level actor that conducts business in this environment, whose objective is to make a profit. In this system, a RebelGroup may choose to extort money from Enterprises in order to support its fighting efforts. It can extract payments from an Enterprise, which fears for its safety if it does not pay. This adds some amount of money to the RebelGroup’s resources, and they can return to extort the same Enterprise again. The RebelGroup can also choose to loot the Enterprise instead. This results in gaining all of the Enterprise wealth, but prompts the individual Enterprise to flee, or leave the model. This reduces the available pool of Enterprises available to the RebelGroup for extortion. Following these interactions the RebelGroup can choose to AllocateWealth, or pay its rebel fighters. Depending on the value of its available resources, it can add more rebels or expel some of those which it already has, changing its size. It can also choose to expand over new territory, or effectively increase its number of potential extorting Enterprises. As a response to these dynamics, an Enterprise can choose to Report expansion to another RebelGroup, which results in fighting between the two groups. This system shows how, faced with economic choices, RebelGroups and Enterprises make decisions in war that impact conflict and violence outcomes.
Interplay of actors about the construction of a dam
Christophe Sibertin-Blanc | Published Monday, December 05, 2016 | Last modified Wednesday, May 09, 2018Model of a very serious conflict about the relevance of a dam to impede its construction, between the client, the prime contractor, State, legalist opponents and activist opponents.
SimDrink: An agent-based NetLogo model of young, heavy drinkers for conducting alcohol policy experiments
Nick Scott Michael Livingston Aaron Hart James Wilson David Moore Paul Dietze | Published Friday, September 25, 2015 | Last modified Thursday, October 15, 2015A proof-of-concept agent-based model ‘SimDrink’, which simulates a population of 18-25 year old heavy alcohol drinkers on a night out in Melbourne to provide a means for conducting policy experiments to inform policy decisions.
Active Shooter: An Agent-Based Model of Unarmed Resistance
T Briggs William Kennedy | Published Thursday, December 29, 2016 | Last modified Tuesday, April 04, 2017A NetLogo ABM developed to explore unarmed resistance to an active shooter. The landscape is a generalized open outdoor area. Parameters enable the user to set shooter armament and control for assumptions with regard to shooter accuracy.