About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 24 results security clear
Local soy value chains in northern Ghana
Tim Verwaart | Published Thursday, August 29, 2019The purpose of the simulation is to evaluate alternative interventions by a value chain development program, aiming to improve rural livelihood and food and nutrition security. In northern Ghana, where distrust between the partners can be a problem in the functioning of value chains, the program supports the incorporation of smallholder farmers in soy clusters or agriculture APEX organization (farmers’ co-operatives) with a fair business environment. The goal is to to include the smallholder farmers in a strong value chain and reduce distrust.
Samambaia Basin - Hydro-ABM
Pedro Phelipe Gonçalves Porto | Published Sunday, April 07, 2019 | Last modified Monday, May 06, 2019This model is a tool to support water management on Samambaia Basin. On it you can explore different scenarios of policy, management and externalities that could influence the water uses. (Scenarios already tested include less rain and payment on water use)
Agent-based model of risk behavior in adolescence
N Schuhmacher P Van Geert L Ballato | Published Monday, June 24, 2013 | Last modified Monday, April 08, 2019The computer model simulates the development of a social network (i.e. formation of friendships and cliques), the (dyadic) interactions between pupils and the development of similarities and differences in their behavioral profiles.
A Model to Unravel the Complexity of Rural Food Security
Samantha Dobbie Stefano Balbi | Published Monday, August 22, 2016 | Last modified Sunday, December 02, 2018An ABM to simulate the behaviour of households within a village and observe the emerging properties of the system in terms of food security. The model quantifies food availability, access, utilisation and stability.
OMOLAND-CA: An Agent-Based Modeling of Rural Households’ Adaptation to Climate Change
Atesmachew Hailegiorgis Claudio Cioffi-Revilla Andrew Crooks | Published Tuesday, July 25, 2017 | Last modified Tuesday, July 10, 2018The purpose of the OMOLAND-CA is to investigate the adaptive capacity of rural households in the South Omo zone of Ethiopia with respect to variation in climate, socioeconomic factors, and land-use at the local level.
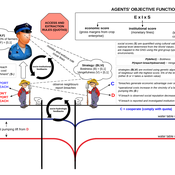
The Regional Security Game: An Agent-based, Evolutionary Model of Strategic Evolution and Stability
Anthony Skews | Published Saturday, June 09, 2018The Regional Security Game is a iterated public goods game with punishement based on based on life sciences work by Boyd et al. (2003 ) and Hintze & Adami (2015 ), with modifications appropriate for an international relations setting. The game models a closed regional system in which states compete over the distribution of common security benefits. Drawing on recent work applying cultural evolutionary paradigms in the social sciences, states learn through imitation of successful strategies rather than making instrumentally rational choices. The model includes the option to fit empirical data to the model, with two case studies included: Europe in 1933 on the verge of war and south-east Asia in 2013.
Market for Protection
Steven Doubleday | Published Monday, July 01, 2013 | Last modified Monday, August 19, 2013Simulation to replicate and extend an analytical model (Konrad & Skaperdas, 2010) of the provision of security as a collective good. We simulate bandits preying upon peasants in an anarchy condition.
The Groundwater Commons Game
Juan Carlos Castilla-Rho Rodrigo Rojas | Published Thursday, May 11, 2017 | Last modified Saturday, September 16, 2017The Groundwater Commons Game synthesises and extends existing work on human cooperation and collective action, to elucidate possible determinants and pathways to regulatory compliance in groundwater systems globally.
This model was design to test parameters that affects the number of people shot during mass shooting. This basic formulation places a gunman in a crowd and allows the users to manipulate parameters of the gunman.
The purpose of this model is to enhance a basic ABM through a simple set of rules identified using the activity-driven models in order to produce more realistic patterns of pedestrian movement.
Displaying 10 of 24 results security clear